EID-EXP-007 – Evidence
Experiment ID: EID-EXP-007
Category: Conditional Access / Identity Protection
Title: Block High-Risk Sign-ins
Result: High-risk sign-ins are blocked via Conditional Access
Risk Rating: High
Evidence Scope
This experiment shows that Microsoft Entra Conditional Access blocks sign-ins classified as High risk by Identity Protection. Without enforcement, high-risk sign-ins may succeed, increasing the risk of credential abuse and attacks.This evidence documents enforcement through Conditional Access and includes sign-in logs that show access is denied when risk signals are detected.
Tenant Conditions
- Entra ID tenant with P2 licensing
- Identity Protection enabled
- Test user group configured for policy targeting
- Break-glass admin account excluded from enforcement
- Conditional Access policy targeting high sign-in risk
Tenant Validation 007-01
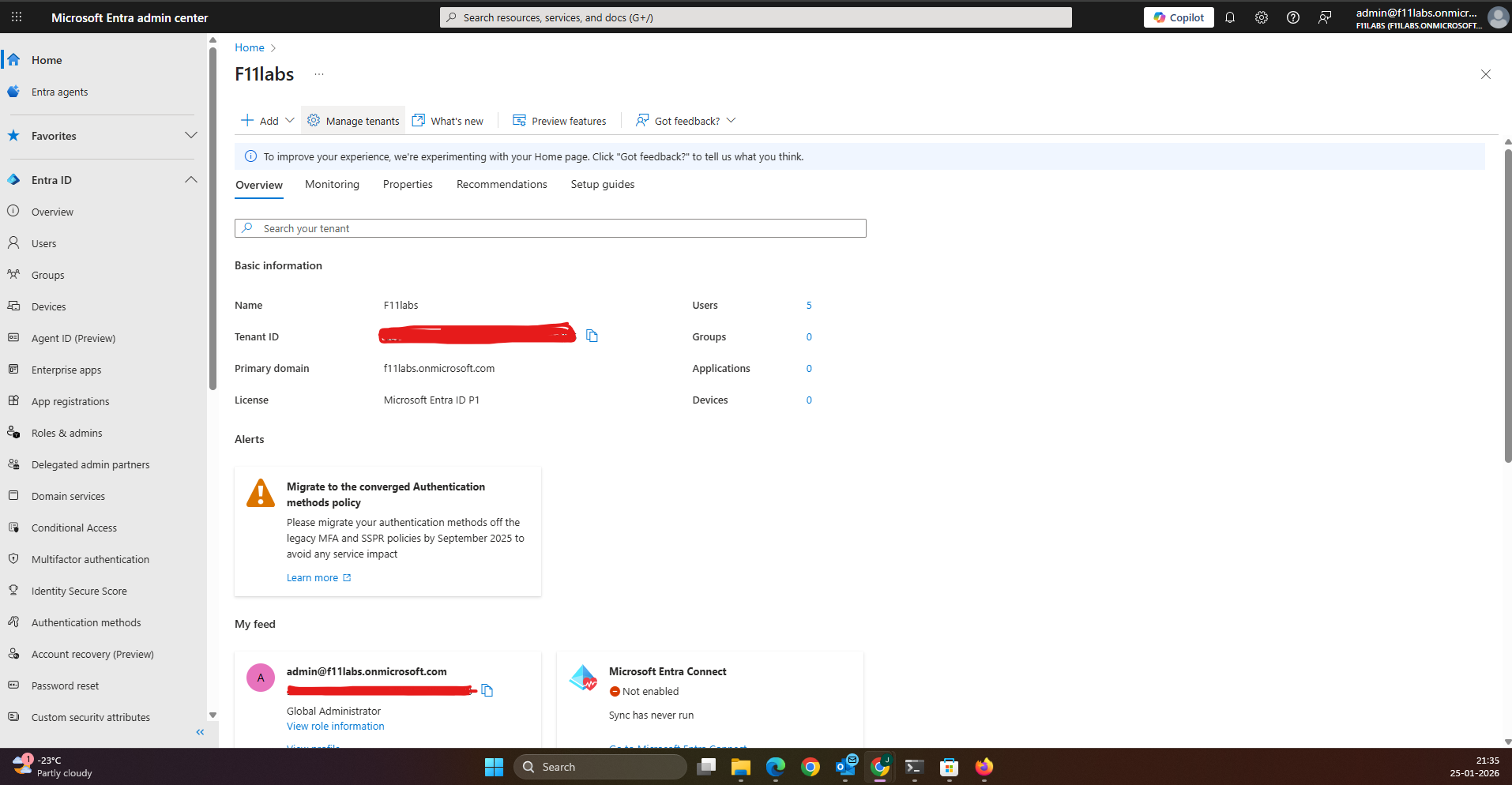
All evidence in this experiment was collected from the Microsoft Entra ID tenant**F11labs** with primary domain **f11labs.onmicrosoft.com**.
Configuration Evidence & Observations
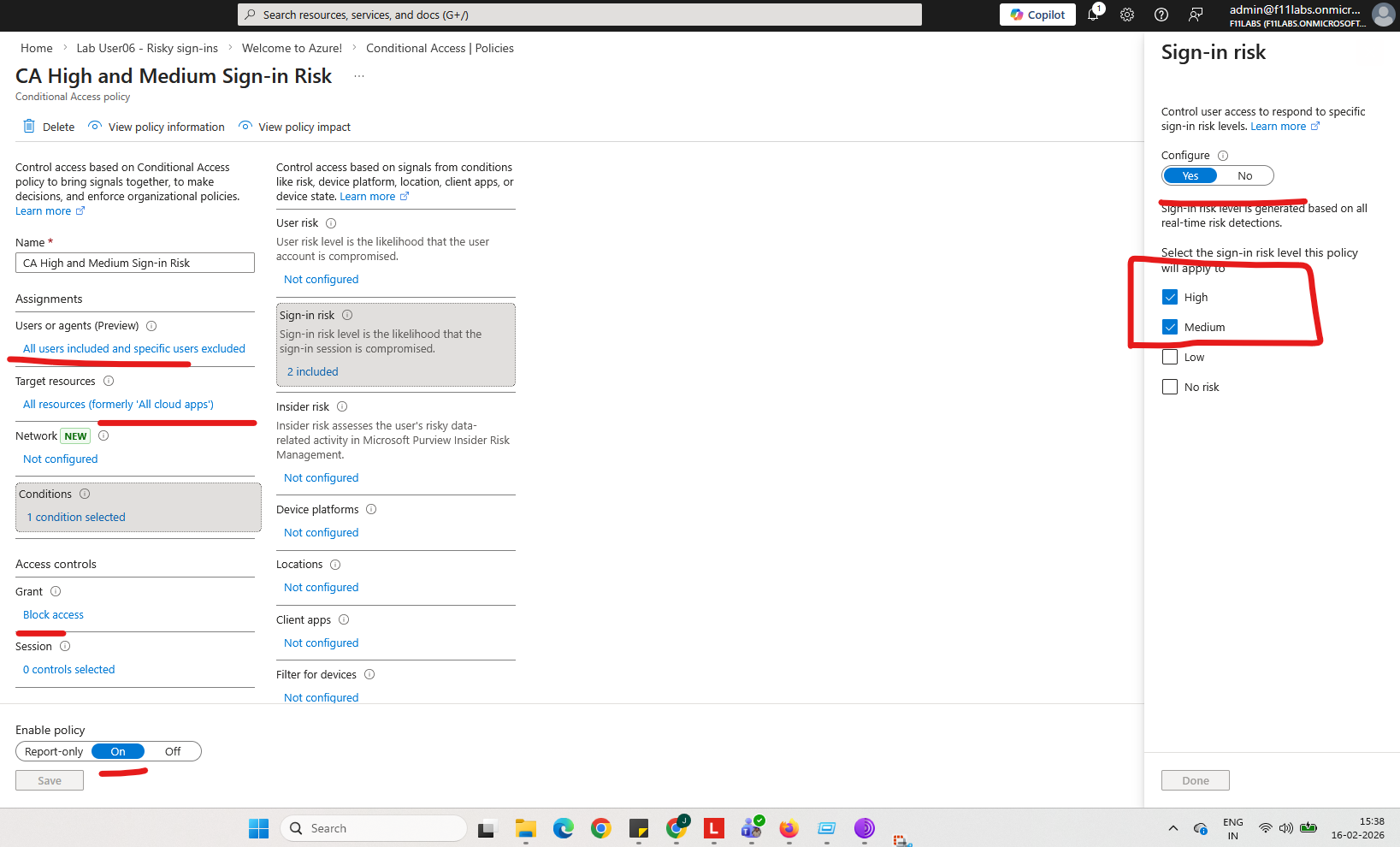
EID-EXP-007-02 – Conditional Access Policy Setup
A Conditional Access policy named EID-EXP-007 (Block High-Risk Sign-ins) was created with the following configuration:
- Users: Test group only
- Cloud apps: All cloud apps
- Conditions: Sign-in risk = High
- Grant: Block access
Observation: The policy is enabled and evaluated for the targeted group.
Impact: High-risk sign-in attempts trigger policy evaluation and enforcement.
Artifact: Screenshot of policy settings (Block High-Risk Sign-ins).
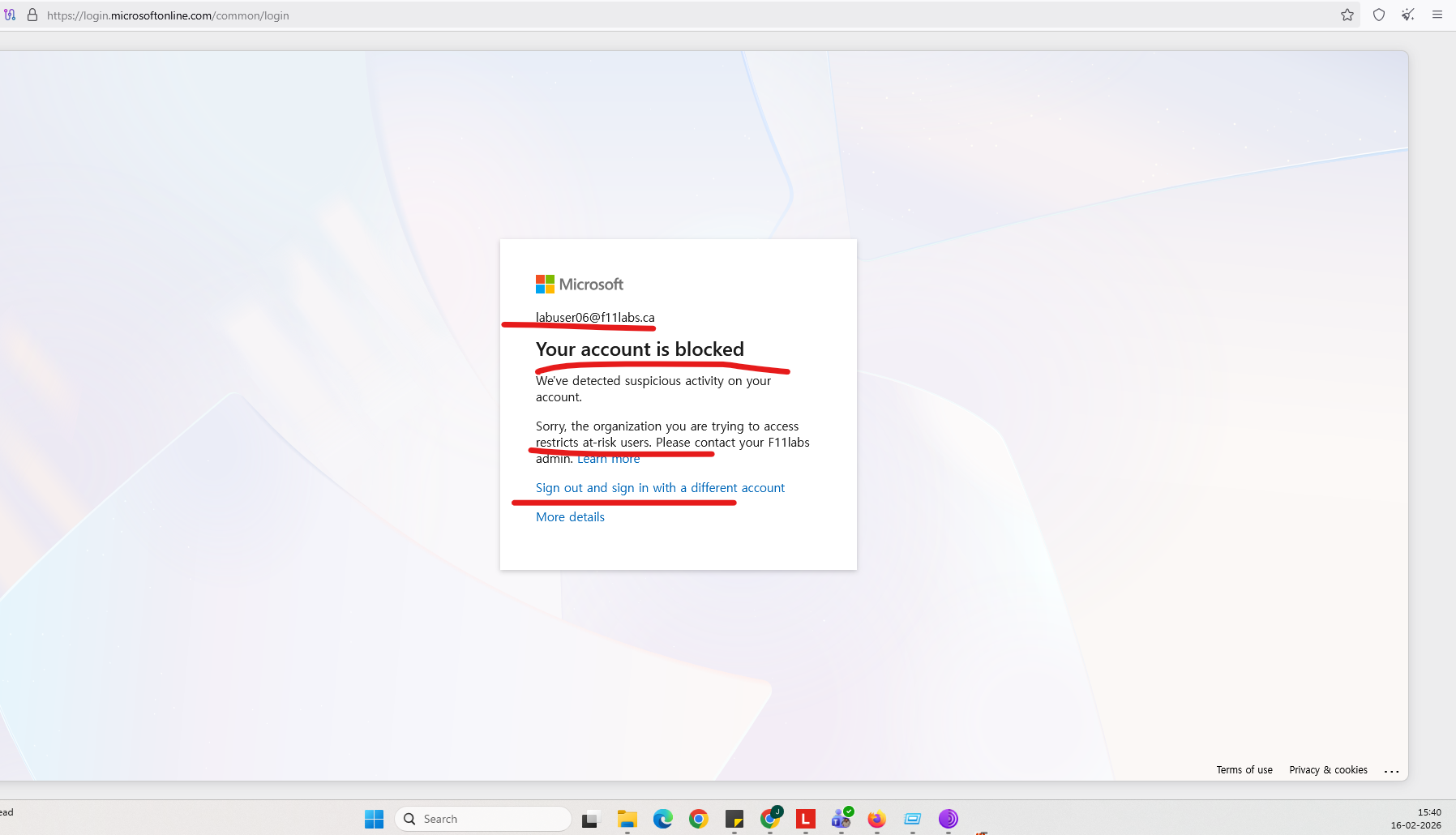
EID-EXP-007-03 – Sign-in Blocked for High Risk
After policy enforcement, a sign-in attempt flagged as High risk was recorded.
Observation:
- Conditional Access status = Failure
- Result = Blocked
- Policy applied = EID-EXP-007
Impact: Access was denied automatically, preventing the risky connection.
Artifact: Sign-in log details showing “Policy result — Blocked”.
Evidence Summary
| 007-01 | Tenant Validation | Informational |
| 007-02 | Conditional Access Policy | Enforced |
007-03 | Sign-in Risk Enforcement | Blocked |
Evidence-Based Conclusion
This experiment confirms that Microsoft Entra Conditional Access automatically blocks sign-ins classified as High risk by Identity Protection. The policy accurately evaluates sign-in signals, denies access, and generates clear, audit-ready logs.
Without this enforcement, high-risk sign-ins may succeed even when detected by Identity Protection, which reduces the tenant’s overall security posture.
Related Analysis & Fix Guidance
- Technical deep dive: High Sign-in Risk in Microsoft Entra: How the Evaluation Engine Really Works
- MSP risk & business impact: Why SMBs Should Block High-Risk Sign-ins in Microsoft 365 (Before It Costs You)
- Video walkthrough: Block High-Risk Sign-ins in Microsoft Entra (Conditional Access Lab)