EID-EXP-008- MFA Fatigue Simulation vs Identity Risk Detection
Category: Authentication
Platform: Microsoft Entra ID
Description: Repeated MFA push requests against a valid user account
Result: MFA repetition alone did not consistently trigger elevated identity risk
Risk: 🟠 Medium
Tenant Conditions
The experiment was performed in a dedicated Microsoft 365 lab tenant.
| Component | Configuration |
|---|---|
| Tenant | Microsoft 365 E5 |
| Identity Platform | Microsoft Entra ID |
| Risk Detection | Identity Protection |
| Access Control | Conditional Access |
| Authentication Method | Microsoft Authenticator push |
| Test User | Standard user with MFA registered |
Scenario Tested
A repeated MFA push attack was simulated against a valid user account.
Attack sequence:
Attacker signs in using valid credentials.
MFA push notification is generated.
User denies or ignores the request.
Attacker repeats authentication attempts.
Test parameters:
10–15 authentication attempts
Multiple attempts within a short time window
Same user account repeatedly targeted
Additional variations were introduced:
alternate IP address (VPN)
browser/device attribute change
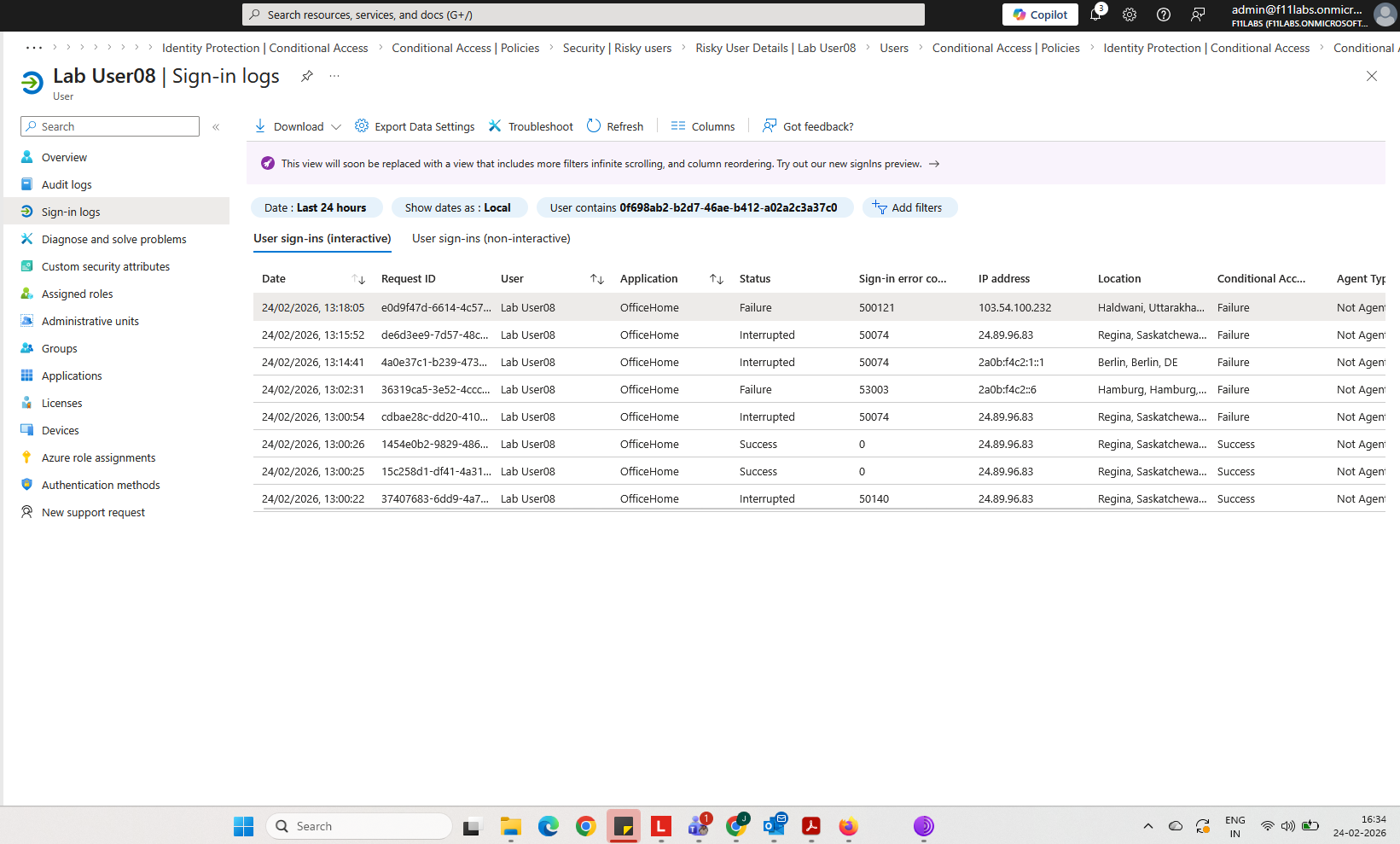
Evidence-01 — Repeated MFA Challenges in Sign-In Logs
Authentication logs show repeated sign-in attempts for the same user within a short time window.
Evidence observed:
multiple authentication attempts
repeated MFA challenges
authentication requirement = MFA
Screenshot reference: Sign-In Logs – Multiple MFA challenges
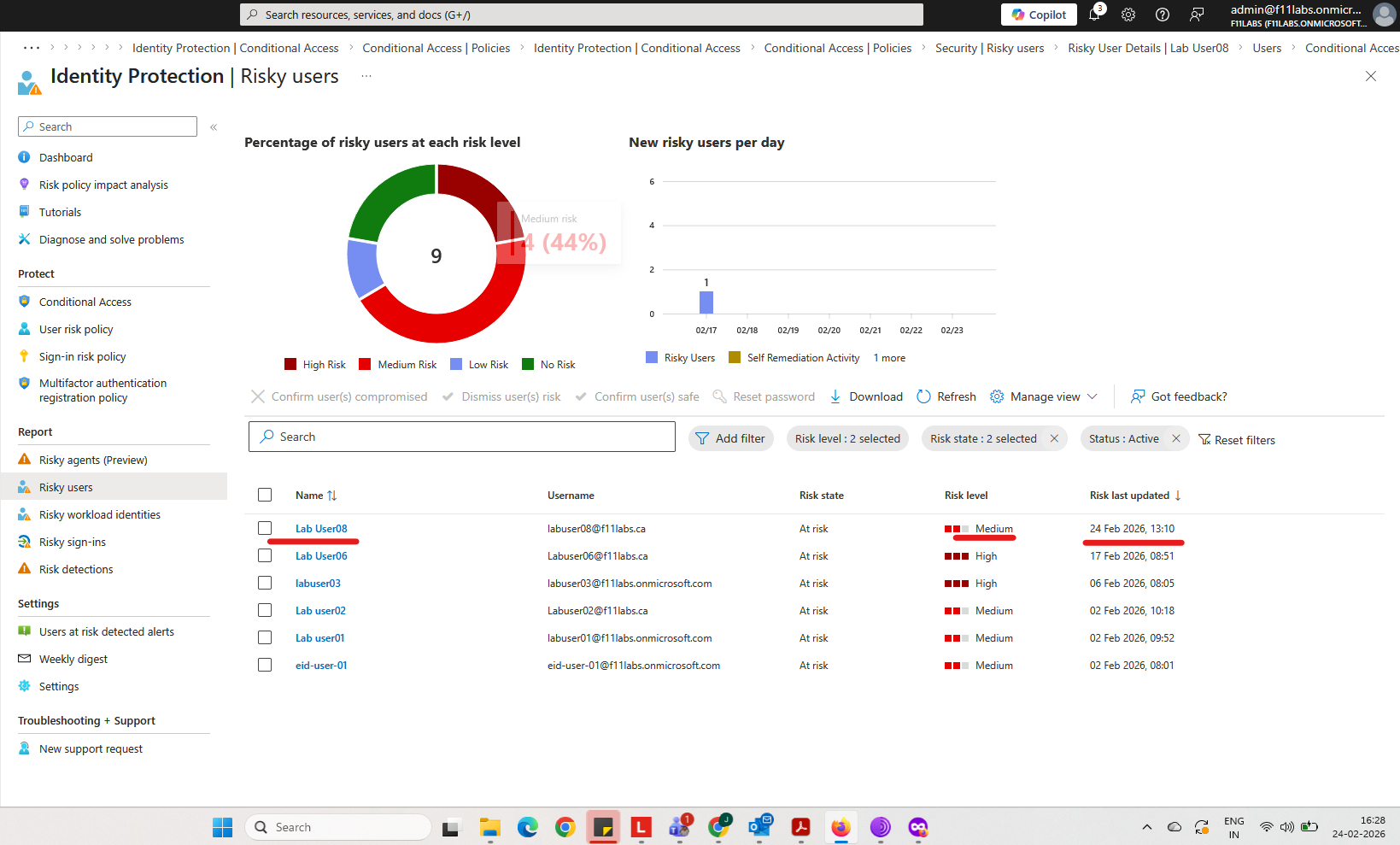
Evidence-02 — Identity Protection Risk Detection
Identity Protection telemetry shows risk signals generated when additional anomalies are introduced.
Evidence observed:
unfamiliar sign-in properties
unusual IP location
elevated sign-in risk
Screenshot reference: Risky Sign-In Detection
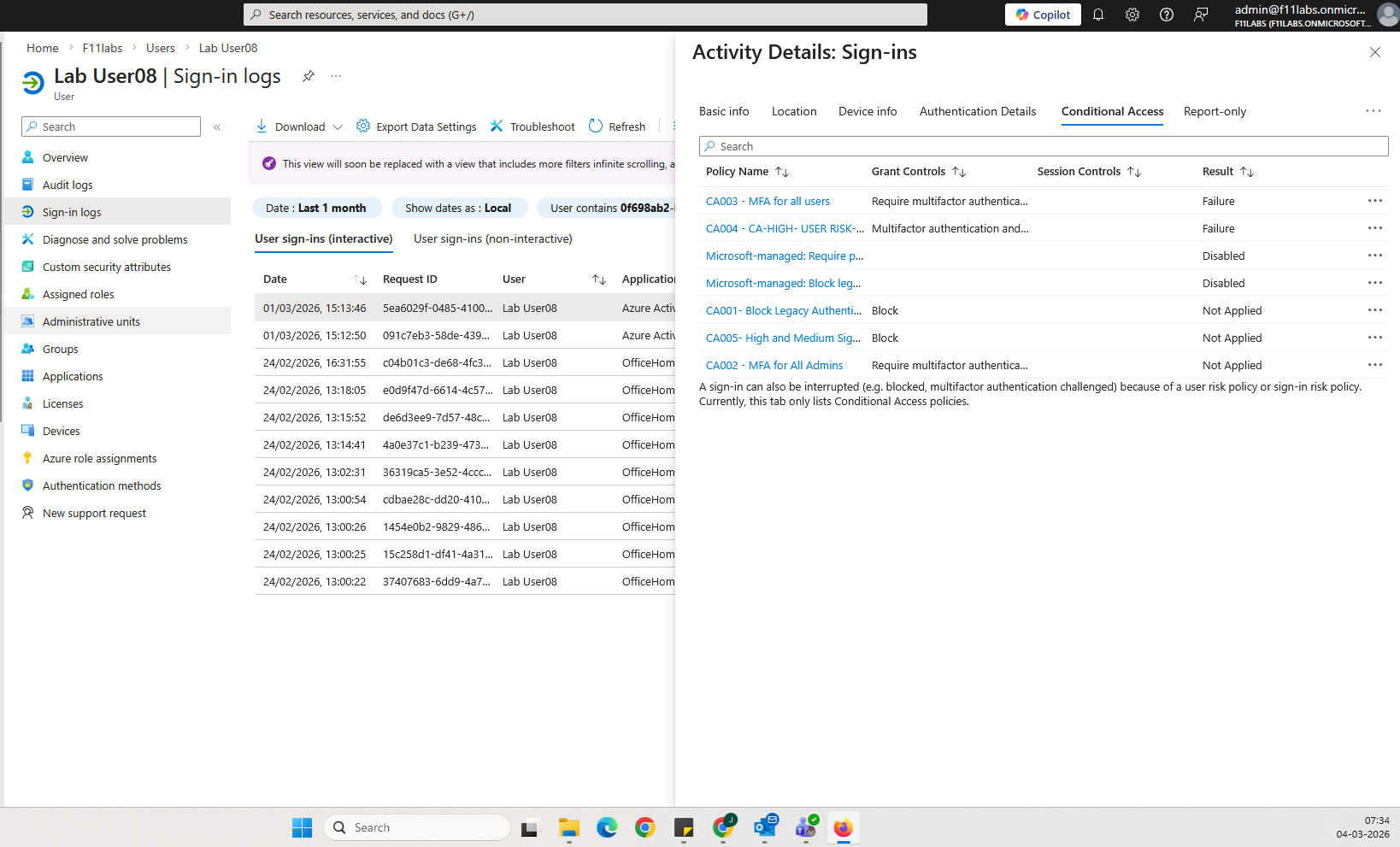
Evidence-03 — Conditional Access Policy Evaluation
Conditional Access logs confirm policy evaluation during elevated sign-in risk events.
Evidence observed:
risk-based policy evaluation
MFA enforcement
Login blocked remediation when user risk escalates
Screenshot reference: Conditional Access Result
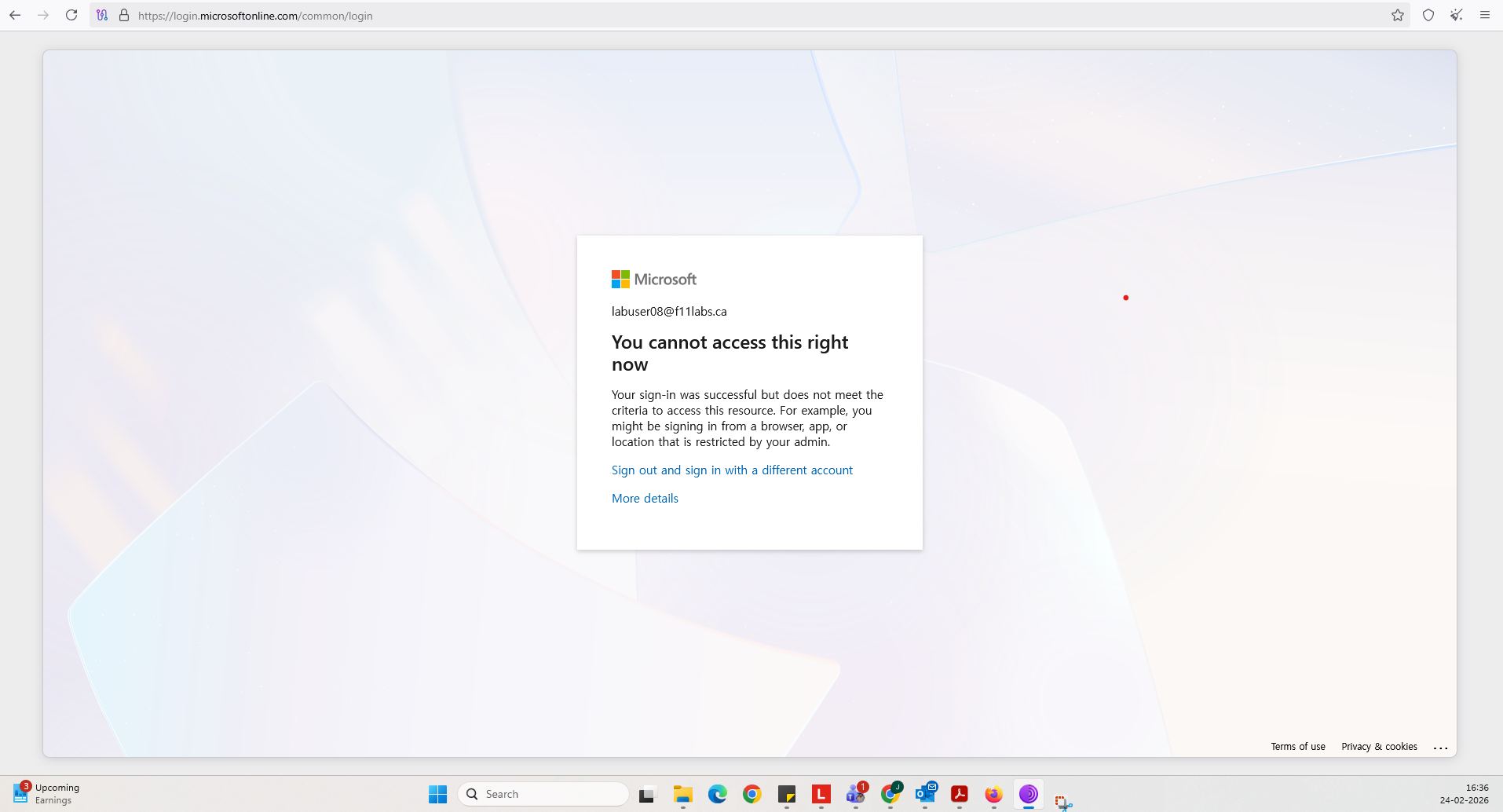
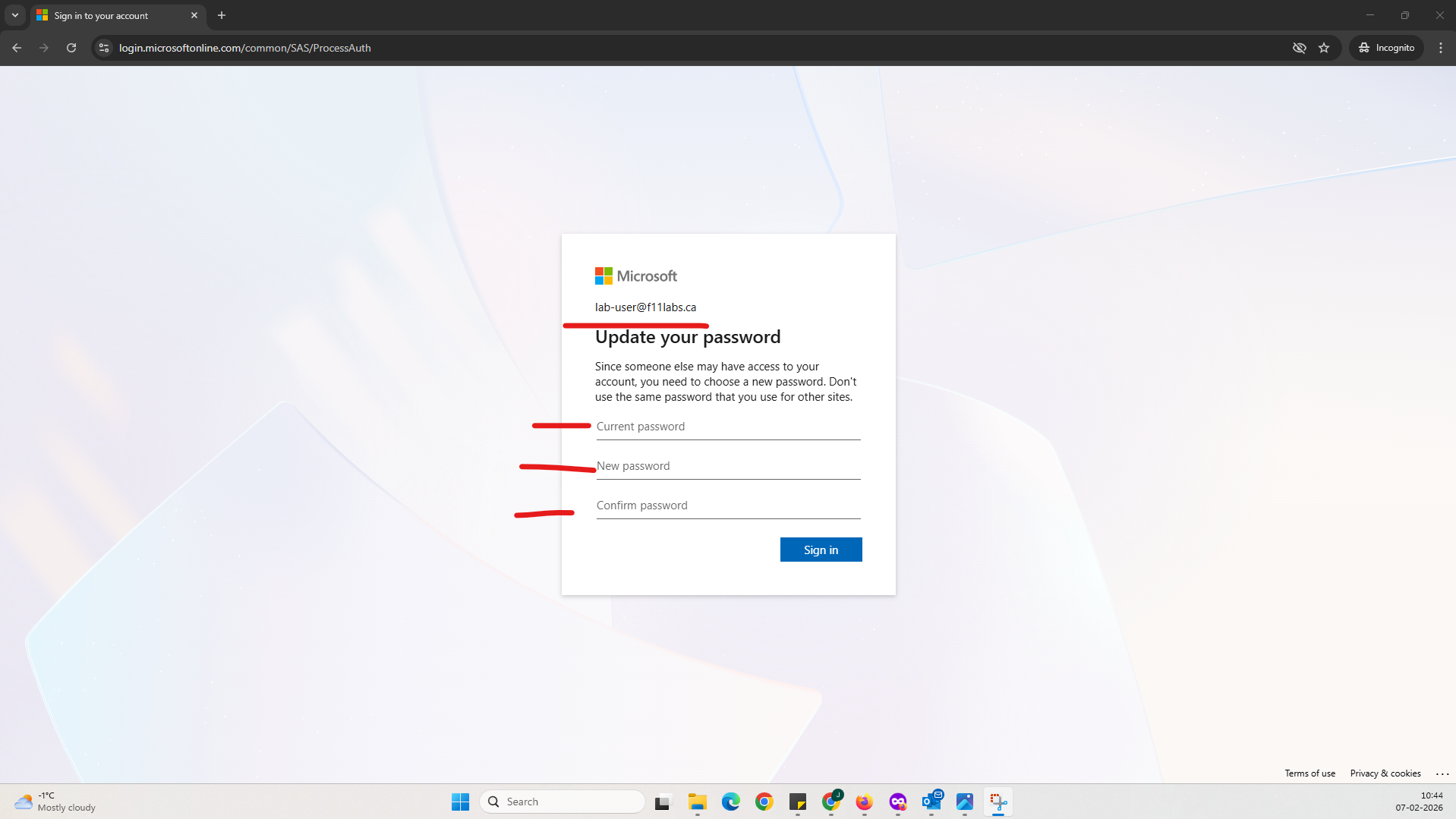
Evidence-04 — User Risk Remediation Trigger
When identity risk escalated during the experiment, remediation policies were triggered.
Observed behavior:
user marked as High risk
password reset requirement enforced
access remediation required before further sign-in attempts
This confirms automated remediation functionality when user risk policies are enabled.
Evidence Summary
| 008-01 | Tenant Validation | Informational |
| 008-02 | Sign-in Logs | High |
008-03 | Sign-in Risk Detection | High |
008-04 | Conditional Access Policy Evaluation | High |
008-05 | User Risk Remediation Trigger | High |
Security Takeaway
MFA fatigue attacks highlight a limitation of push-based authentication.
MFA alone does not reliably prevent account compromise.
Effective protection requires:
identity risk detection
risk-based Conditional Access policies
automated remediation workflows
Without these controls, MFA functions primarily as a notification mechanism rather than an automated defense.
Related Analysis & Fix Guidance
- Technical deep dive: MFA Fatigue Attacks in Microsoft 365: Why Risk-Based Conditional Access Is Non-Negotiable
- MSP risk & business impact: MFA Fatigue Attacks: The Overlooked Risk Increasing Business Costs
- Video walkthrough: MFA Fatigue Explained: How Hackers Trick Users Into Approving Attacks