EID-EXP-009 – Evidence
Experiment ID: EID-EXP-009
Category: Hybrid Identity / Security Baseline
Title: Hybrid Identity Security Baseline – Configuration and Visibility Review
Result: Hybrid identity synchronization works immediately, but baseline security controls require explicit configuration
Risk Rating: 🟠 Medium
Evidence Scope
This experiment evaluates the initial security posture of a hybrid identity environment after enabling Microsoft Entra ID synchronization using Azure AD Connect.
The goal of this experiment is to document how identity synchronization, authentication visibility, and baseline security controls appear in Microsoft Entra ID immediately after hybrid identity is established.
The focus is not on attack simulation, but on observing the default configuration state and visibility gaps that may exist before security baselines are fully implemented.
Tenant Conditions:
Microsoft Entra ID tenant (Free or P1)
Hybrid identity enabled via Azure AD Connect
Password Hash Synchronization enabled
Test user synchronized from on-premises Active Directory
Default Conditional Access configuration
Default Microsoft security recommendations not fully implemented
Tenant Validation 001-01
All evidence in this experiment was collected from the Microsoft Entra ID tenant F11labs with primary domain f11labs.onmicrosoft.com.
Evidence Artifact:
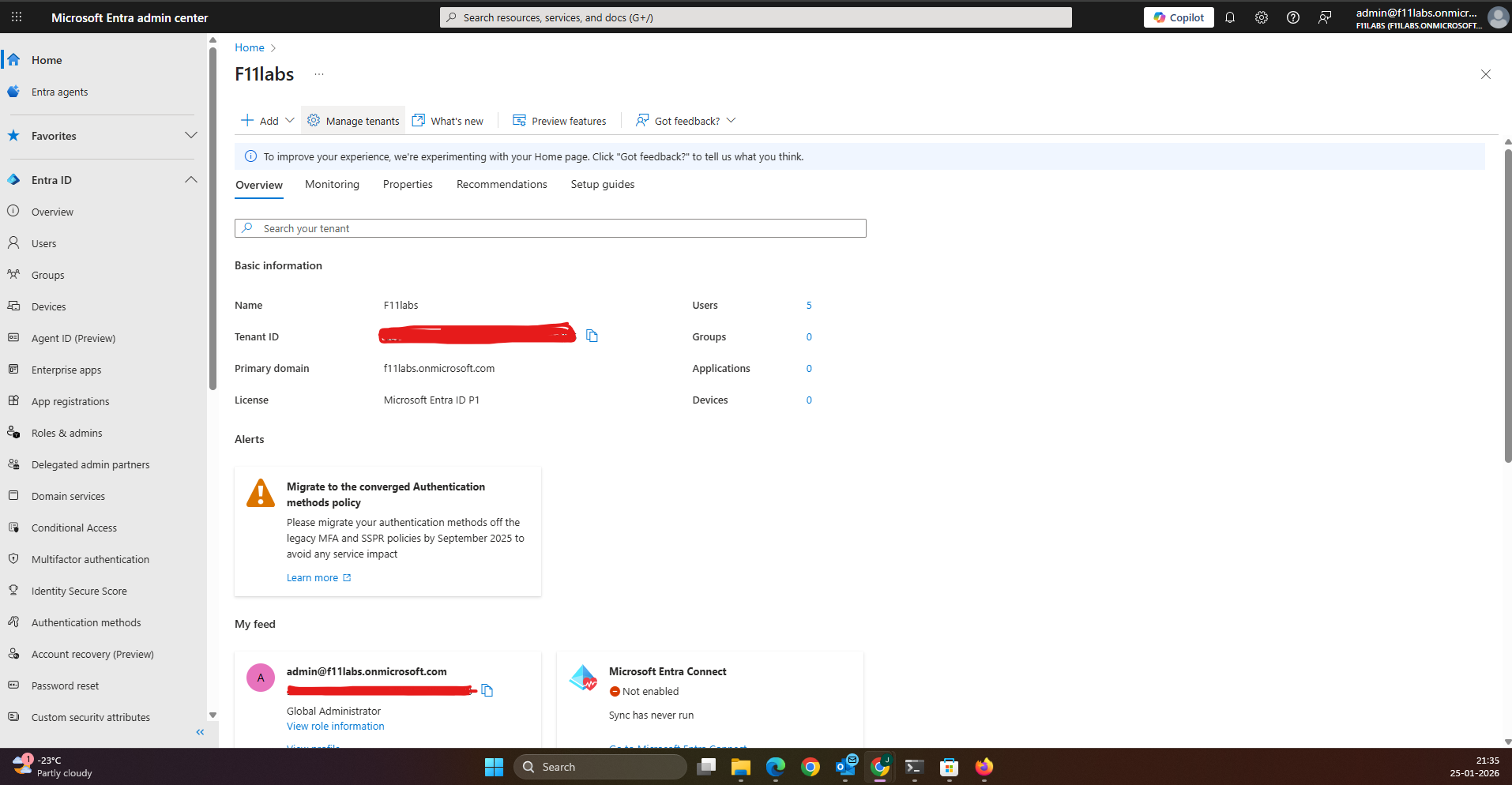
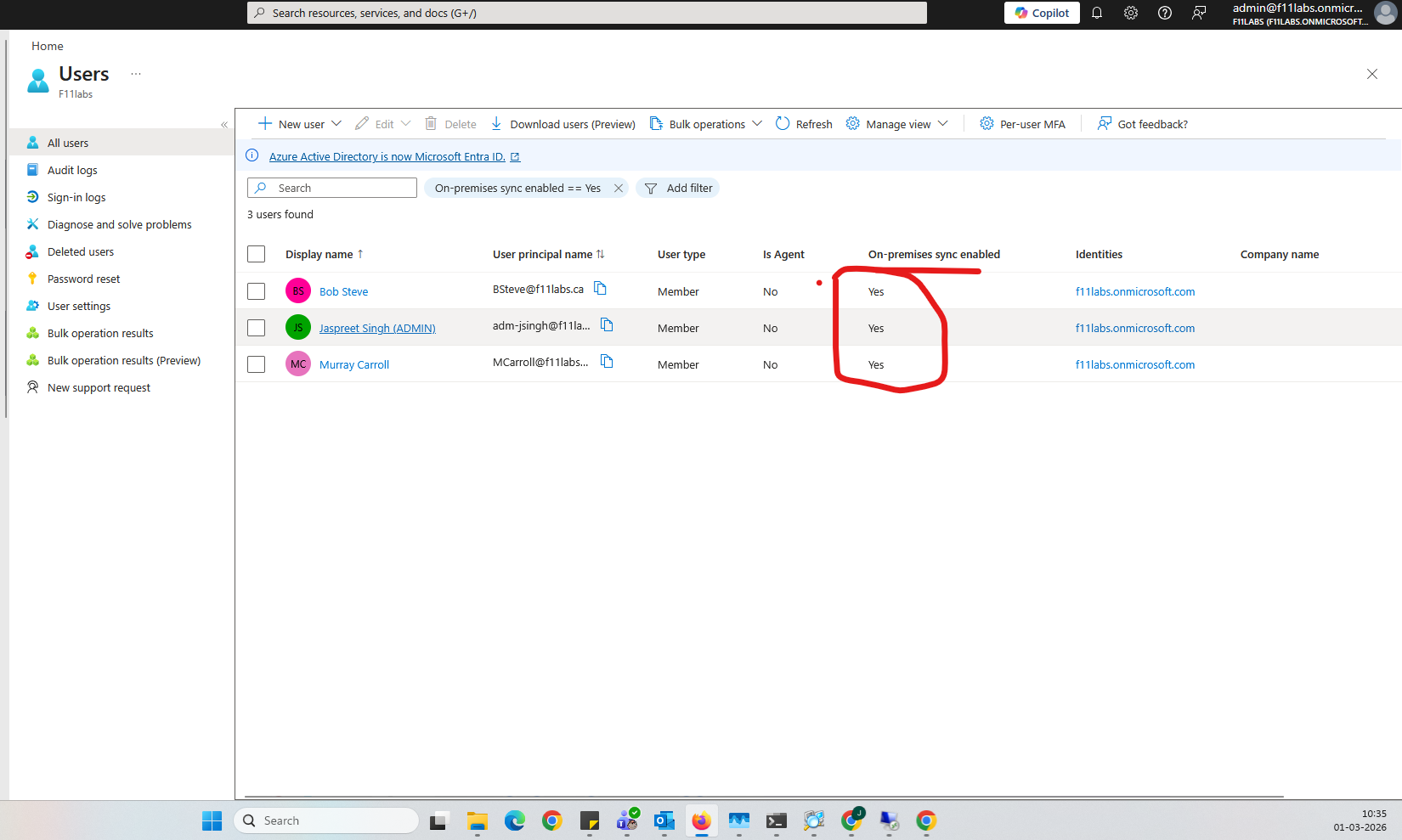
Evidence EID-EXP-009-01 – Successful Directory Synchronization
Control Area: Identity Synchronization
Observation: On-premises Active Directory users appear in Microsoft Entra ID after Azure AD Connect synchronization.
Expected Secure State: Hybrid identities should synchronize successfully and be clearly identified as originating from on-premises Active Directory.
Actual Result: Synchronized accounts appear in Entra ID with the source listed as Windows Server Active Directory.
Impact:
Hybrid identity is operational
User authentication can occur through cloud services
Identity synchronization increases the importance of strong authentication controls
Evidence Artifact: Entra ID user list showing accounts synchronized from on-premises Active Directory.
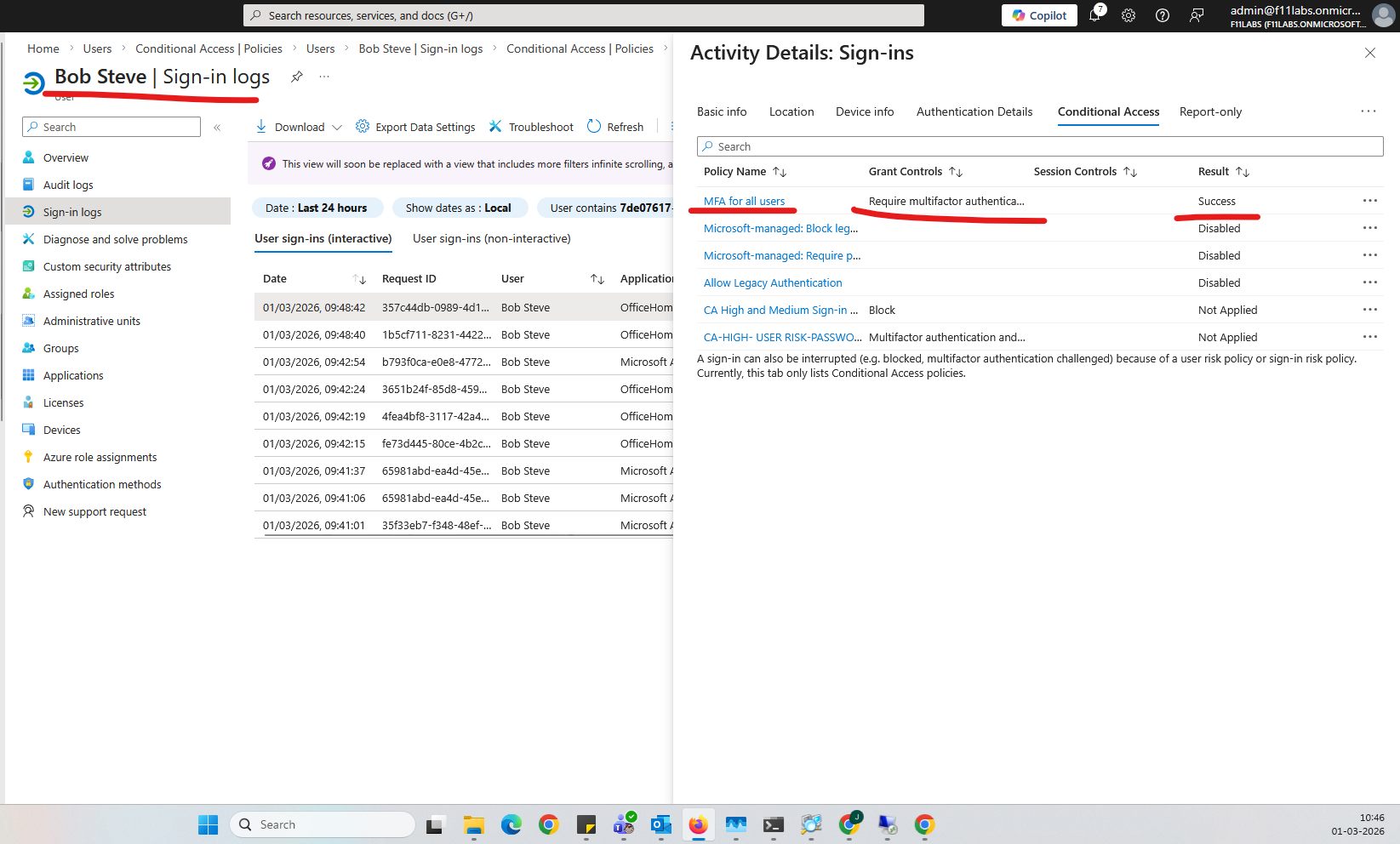
Evidence EID-EXP-009-02 – Authentication Visibility in Sign-In Logs
Control Area: Authentication Monitoring
Observation: User authentication activity appears in Microsoft Entra ID sign-in logs after hybrid synchronization is enabled.
Expected Secure State: Administrators should be able to review authentication activity for hybrid users.
Actual Result: Successful authentication events are recorded in the Entra ID sign-in logs for synchronized users.
Impact:
Authentication activity becomes visible in the Entra monitoring interface
Administrators gain the ability to monitor login behavior
Sign-in logs become a primary investigation source
Evidence Artifact: Entra sign-in logs showing successful authentication from a synchronized hybrid identity.
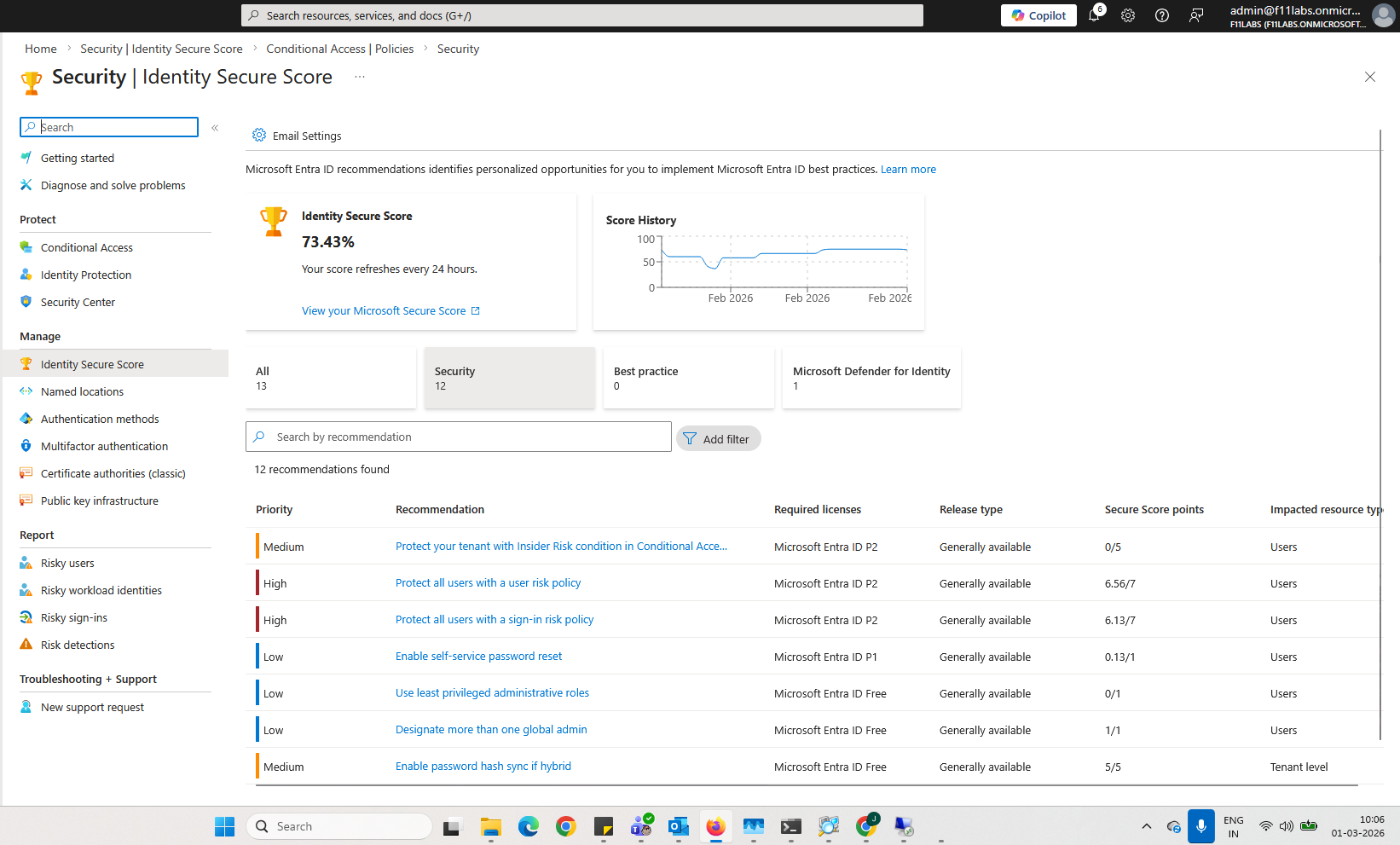
Evidence EID-EXP-009-03 – Baseline Security Recommendations Not Automatically Enforced
Control Area: Security Baseline
Observation: After hybrid identity configuration, several recommended security controls remain optional.
Expected Secure State: Critical identity protections such as strong MFA enforcement and conditional access should be clearly implemented.
Actual Result: Microsoft Entra provides security recommendations through Secure Score, but these controls are not automatically enforced.
Impact:
Organizations may operate with incomplete identity protection
Baseline security controls depend on administrator implementation
Default configuration does not guarantee strong authentication protection
Evidence Artifact: Microsoft Secure Score dashboard showing recommended identity security improvements.
Evidence Summary
009-01 | ||
| 009-01 | Tenant Validation | Informational |
| 009-02 | Sign-in Logs | High |
009-03 | Sign-in Risk Detection | High |
009-04 | Conditional Access Policy Evaluation | High |
0089-05 | User Risk Remediation Trigger | High |
Evidence-Based Conclusion
This experiment confirms that enabling hybrid identity synchronization between Active Directory and Microsoft Entra ID immediately establishes authentication visibility and identity integration.
However, core security protections such as Conditional Access policies, strong MFA enforcement, and baseline security controls require deliberate configuration.
Without implementing these additional controls, organizations may operate in a hybrid identity environment where authentication works correctly but identity protection remains incomplete.
Hybrid identity should therefore always be followed by the implementation of a security baseline to strengthen authentication and monitoring capabilities.
Next Experiment: EID-EXP-010 – Conditional Access Policy Enforcement Validation
Related Analysis & Fix Guidance
- Technical deep dive: Hybrid Identity Security Risks: What Business Leaders Need to Know Before a Breach Happens
- MSP risk & business impact: Hybrid Identity Security: The Hidden Risk Most Businesses Don’t See Until It’s Too Late
- Video walkthrough: SC-300: Building a Secure Hybrid Identity Baseline | Entra ID + Azure AD Connect Lab