EID-EXP-010 – Evidence
Experiment ID: EID-EXP-010
Category: Conditional Access
Title: Conditional Access and Named Locations – Trust Boundary Evaluation
Result: Location-based trust reduces authentication enforcement
Risk Rating: 🔴 High
Evidence Scope
This evidence was collected from a hybrid identity environment that integrates on-premises Active Directory with Microsoft Entra ID.
Tenant Conditions:
- Microsoft Entra ID tenant with Conditional Access enabled
- Azure AD Connect configured (Password Hash Sync)
- Hybrid users synchronized from on-prem Active Directory
- No additional device compliance or risk-based policies configured.
- Named Location configured as a trusted IP range
This experiment assesses how Conditional Access evaluates authentication when Named Locations serve as a trust signal.
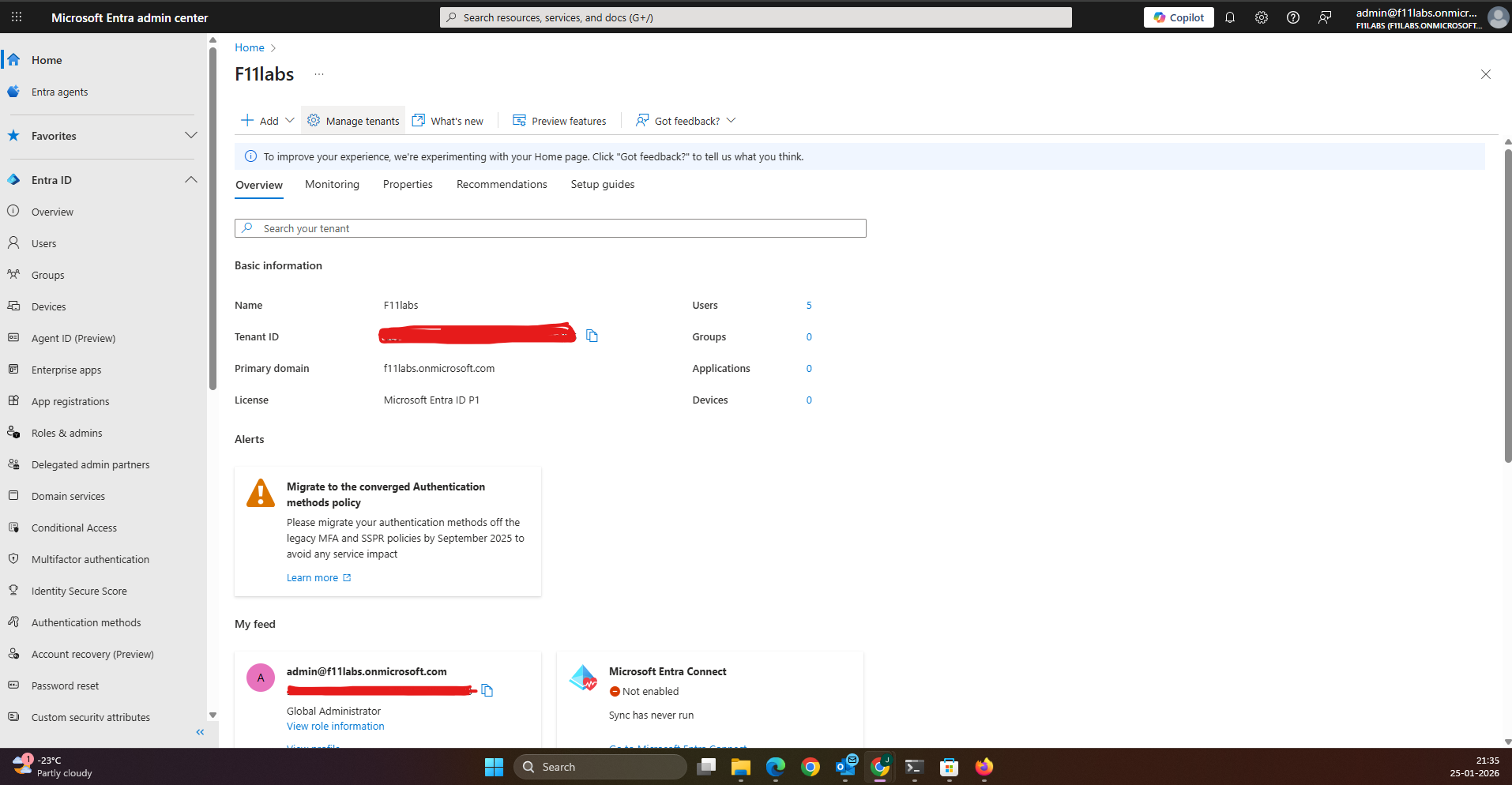
Tenant Validation 010-01
All evidence for this experiment was collected from the Microsoft Entra ID tenant.
The primary domain is f11labs.onmicrosoft.com (F11labs).
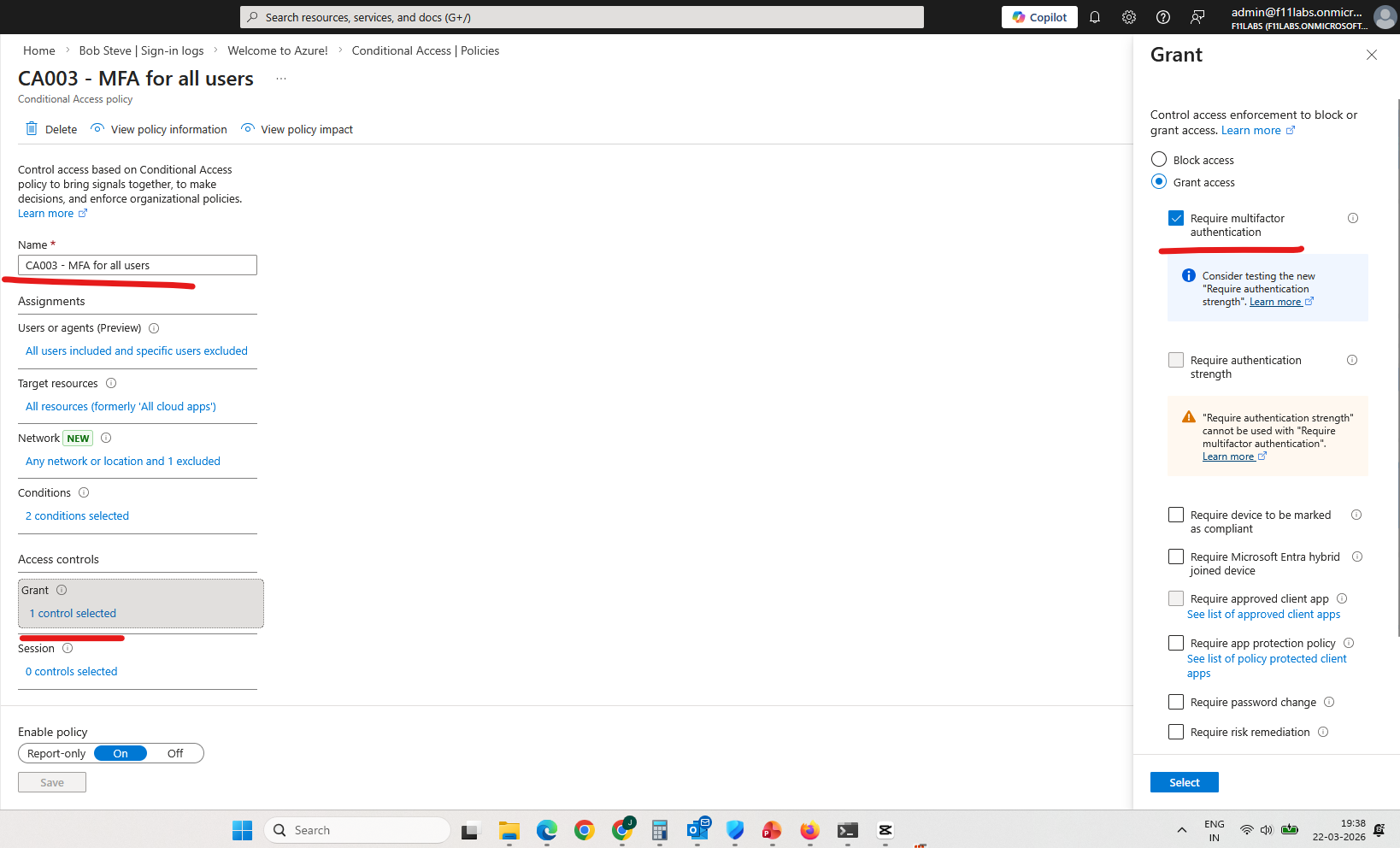
Evidence EID-EXP-010-01
Control Area: Conditional Access Policy Configuration
Observation: The Conditional Access policy enforces MFA only for non-trusted locations.
Expected Secure State: MFA should be consistently enforced regardless of network location.
Actual Result: MFA enforcement is bypassed when authentication originates from a trusted Named Location.
Impact: Authentication strength varies by network location, reducing the consistency of security controls.
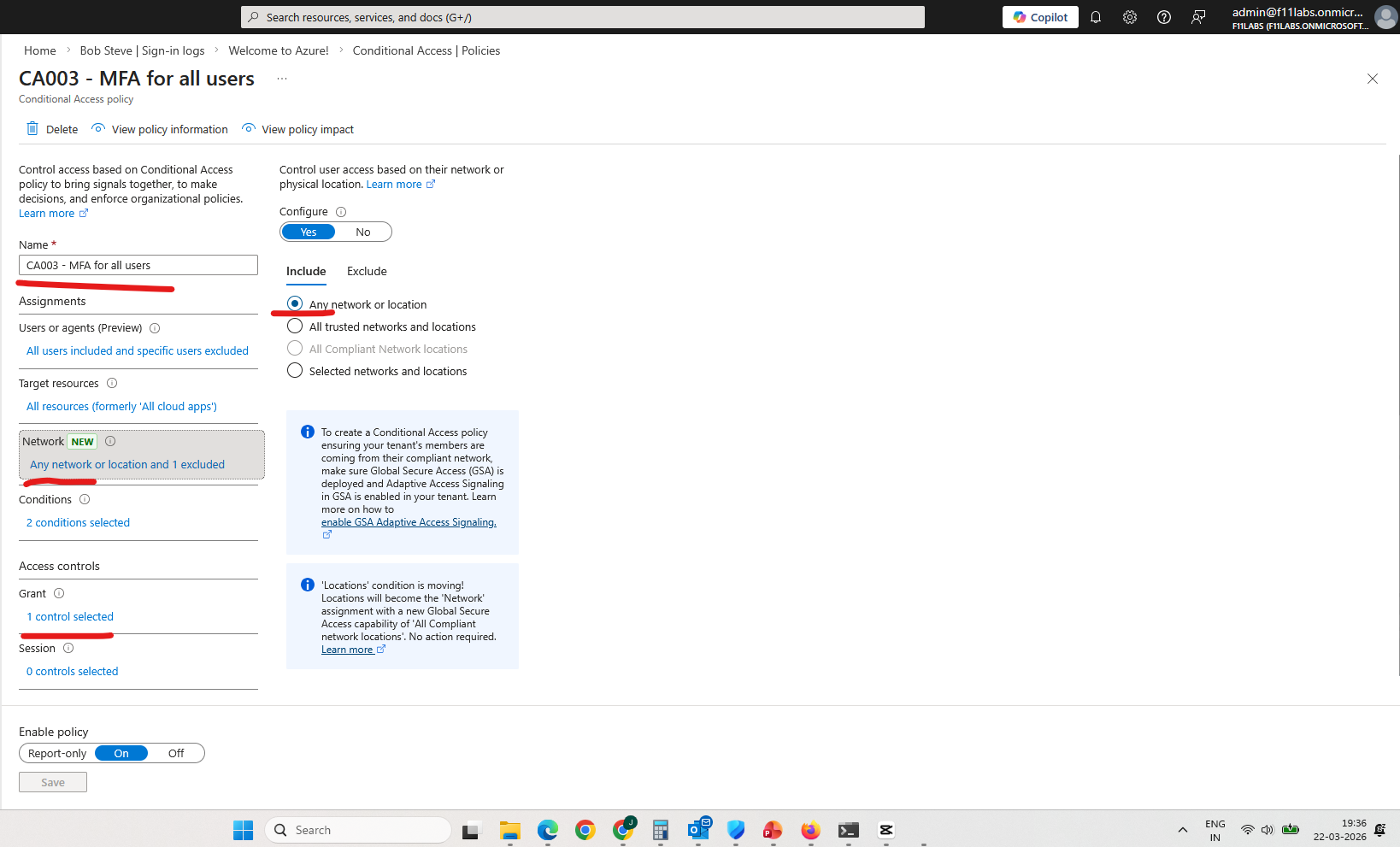
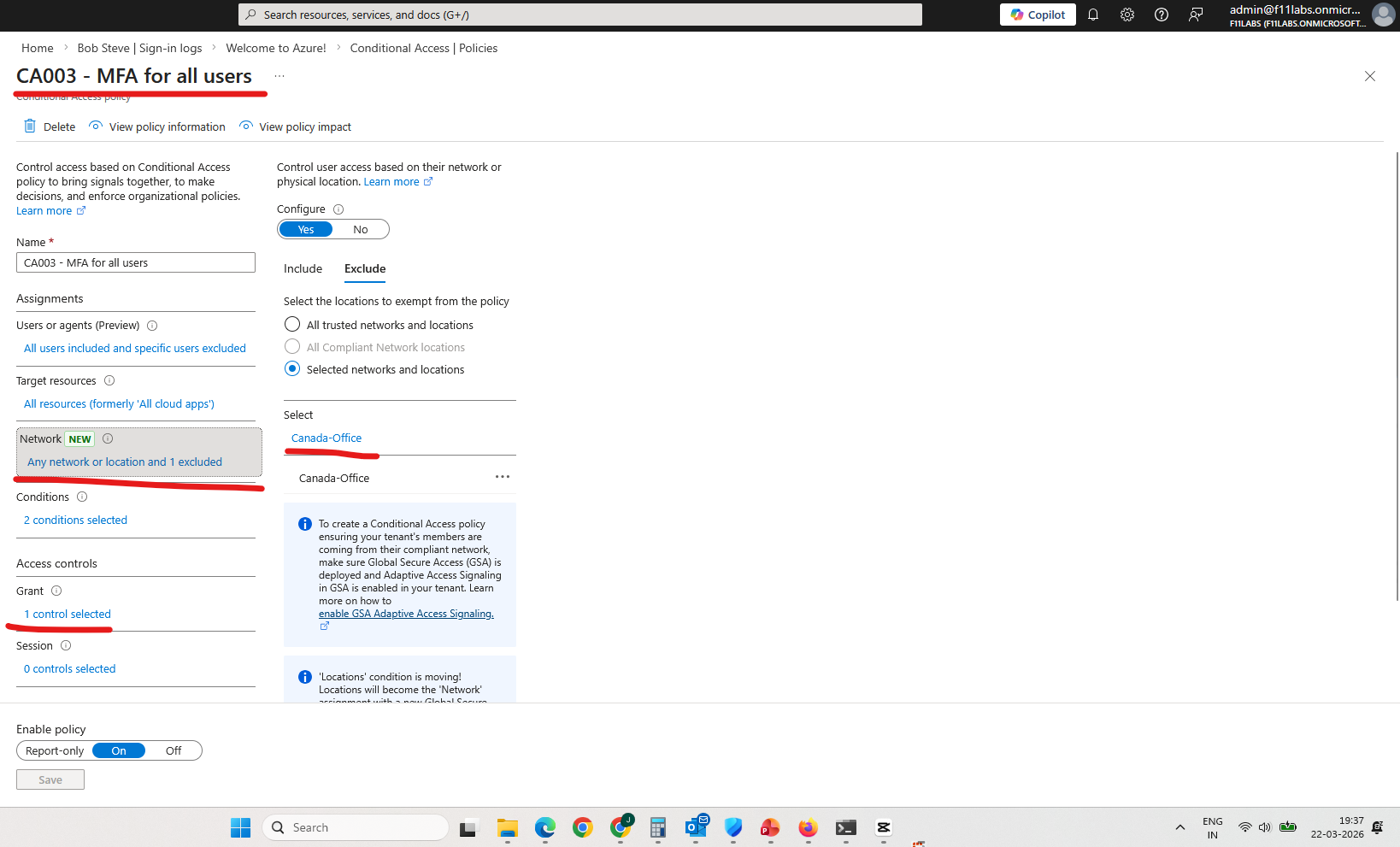
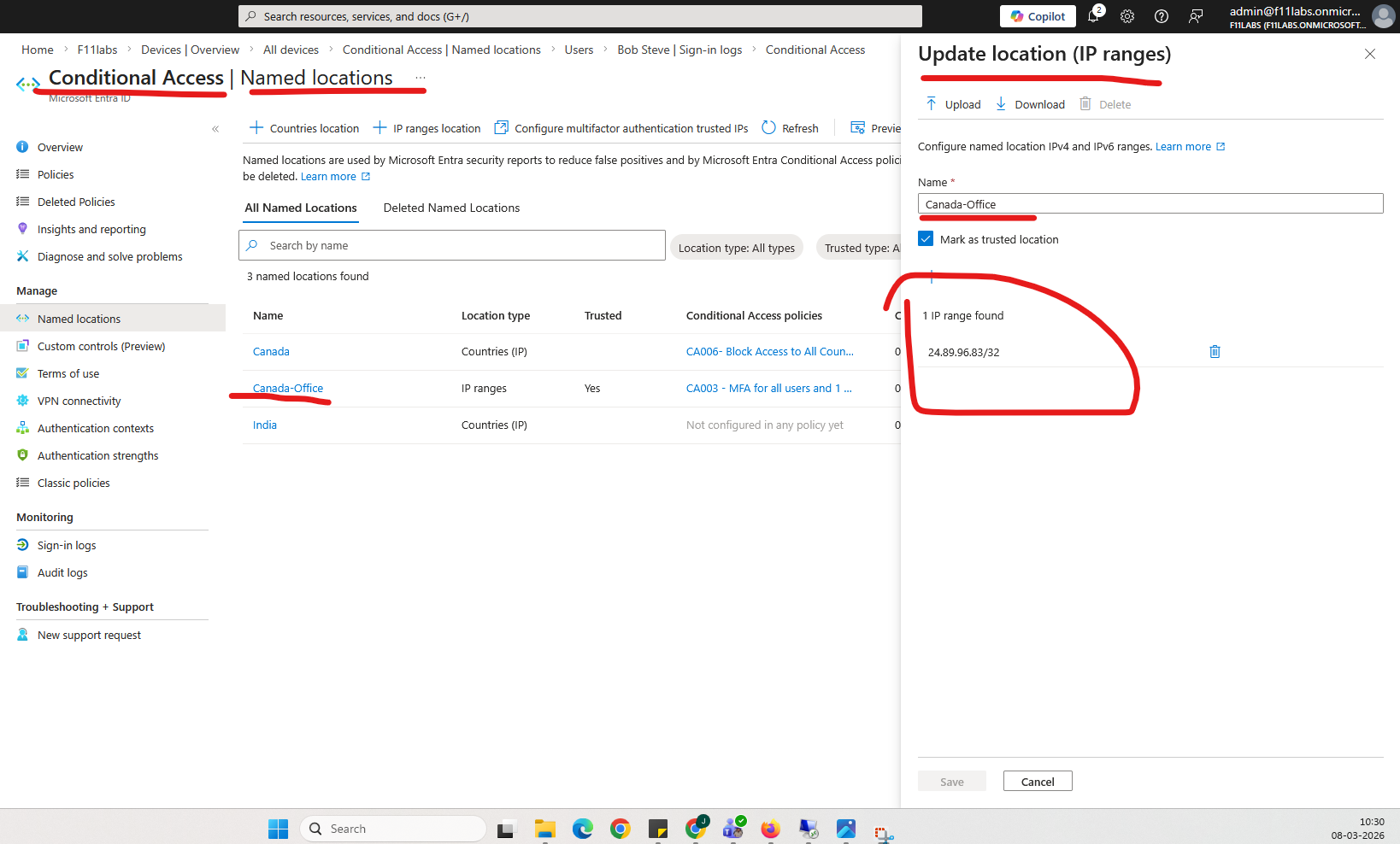
Evidence EID-EXP-010-02
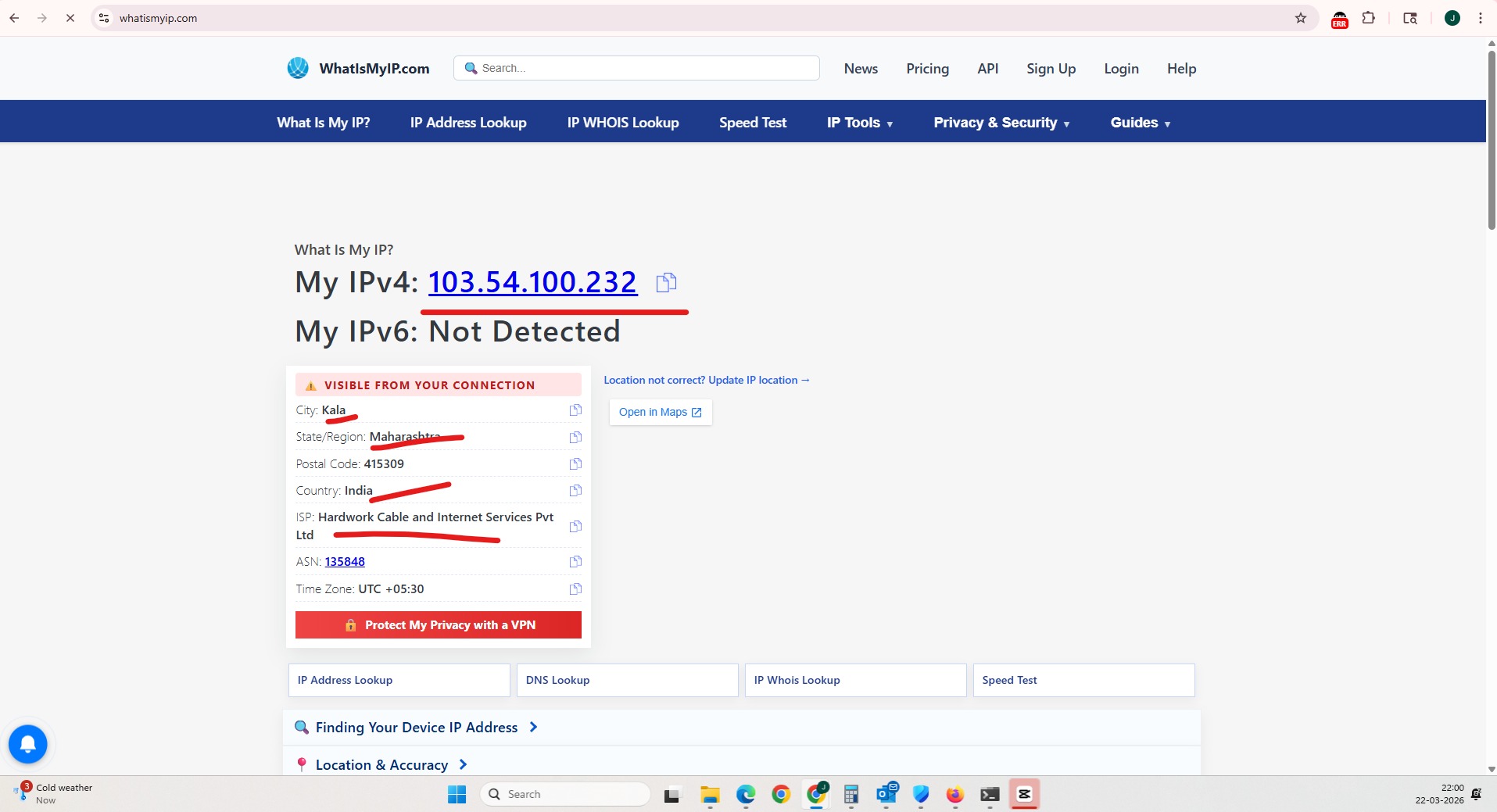
Control Area: Named Locations
Observation: A public IP range is configured as a trusted Named Location.
Expected Secure State: Trusted locations should not reduce authentication requirements without additional validation controls.
Actual Result: Authentication from the trusted IP range is treated as inherently safe.
Impact: Network-based trust introduces implicit assumptions about authentication security.
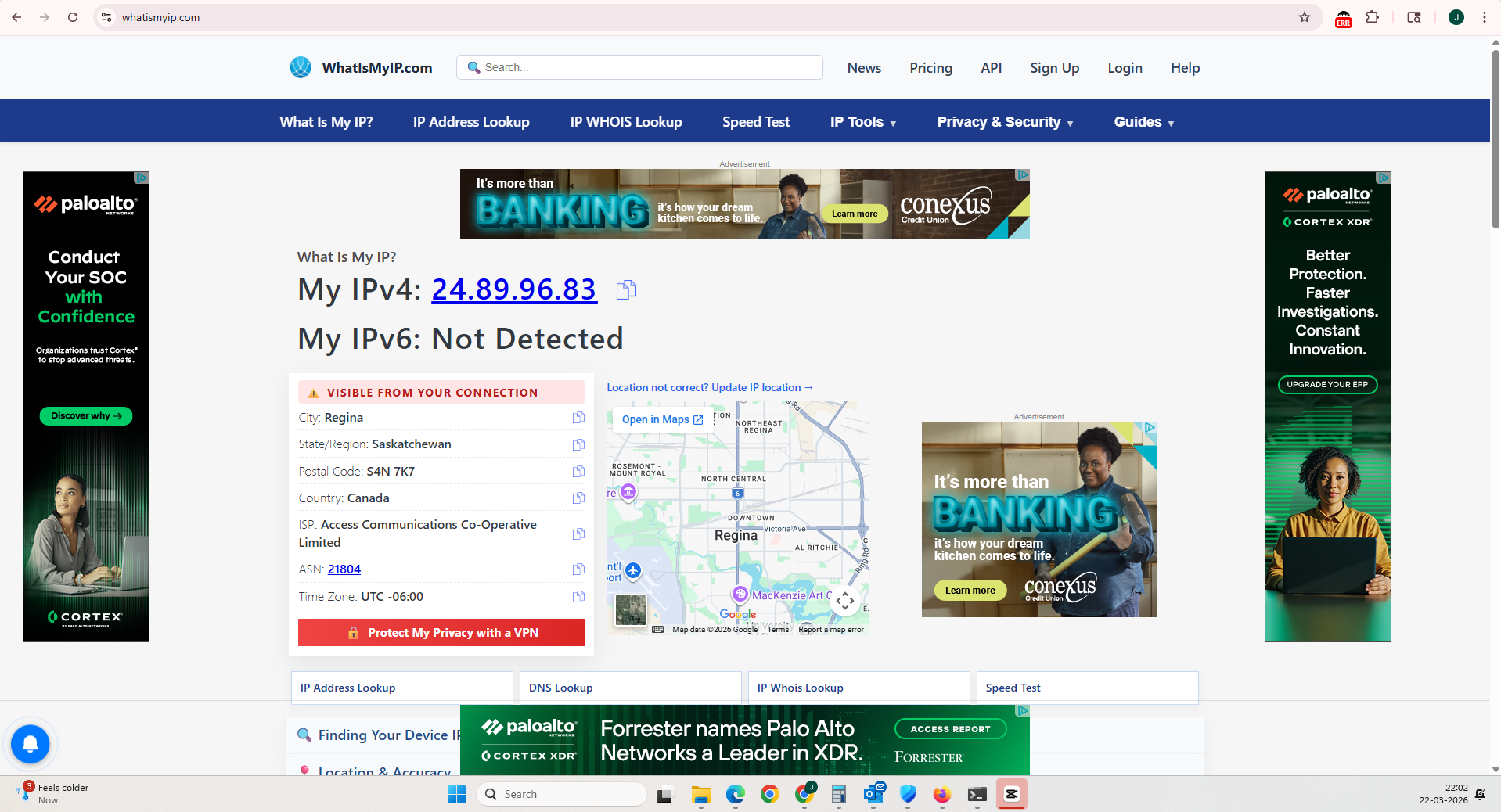
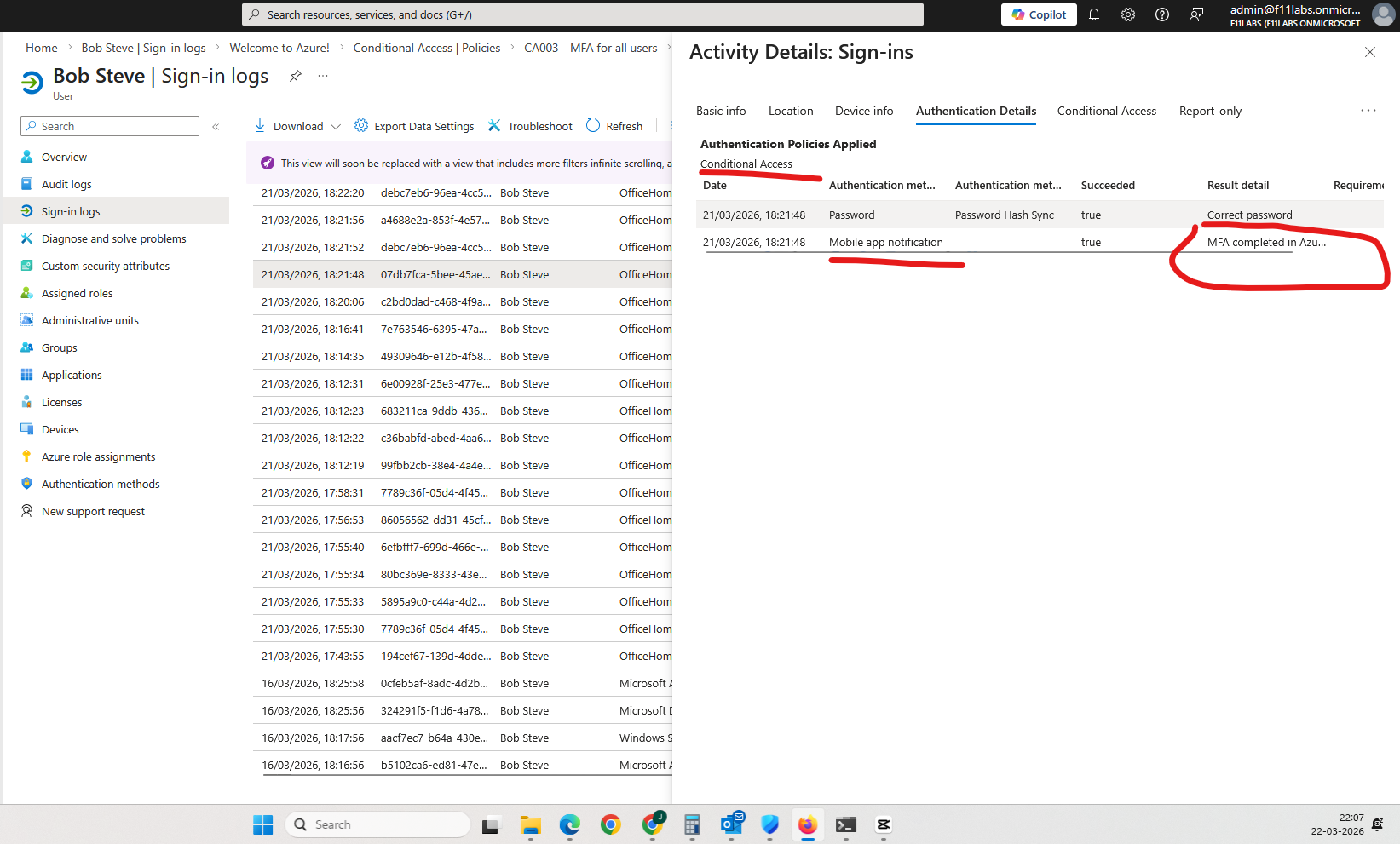
Evidence EID-EXP-010-03
Control Area: Authentication – Trusted Location
Observation: User authentication from a trusted location succeeds without MFA.
Expected Secure State: MFA should be enforced for all interactive sign-ins.
Actual Result: Authentication succeeds without MFA when originating from a trusted network.
Impact: Authentication controls are weakened within trusted locations.
Evidence Artifact:
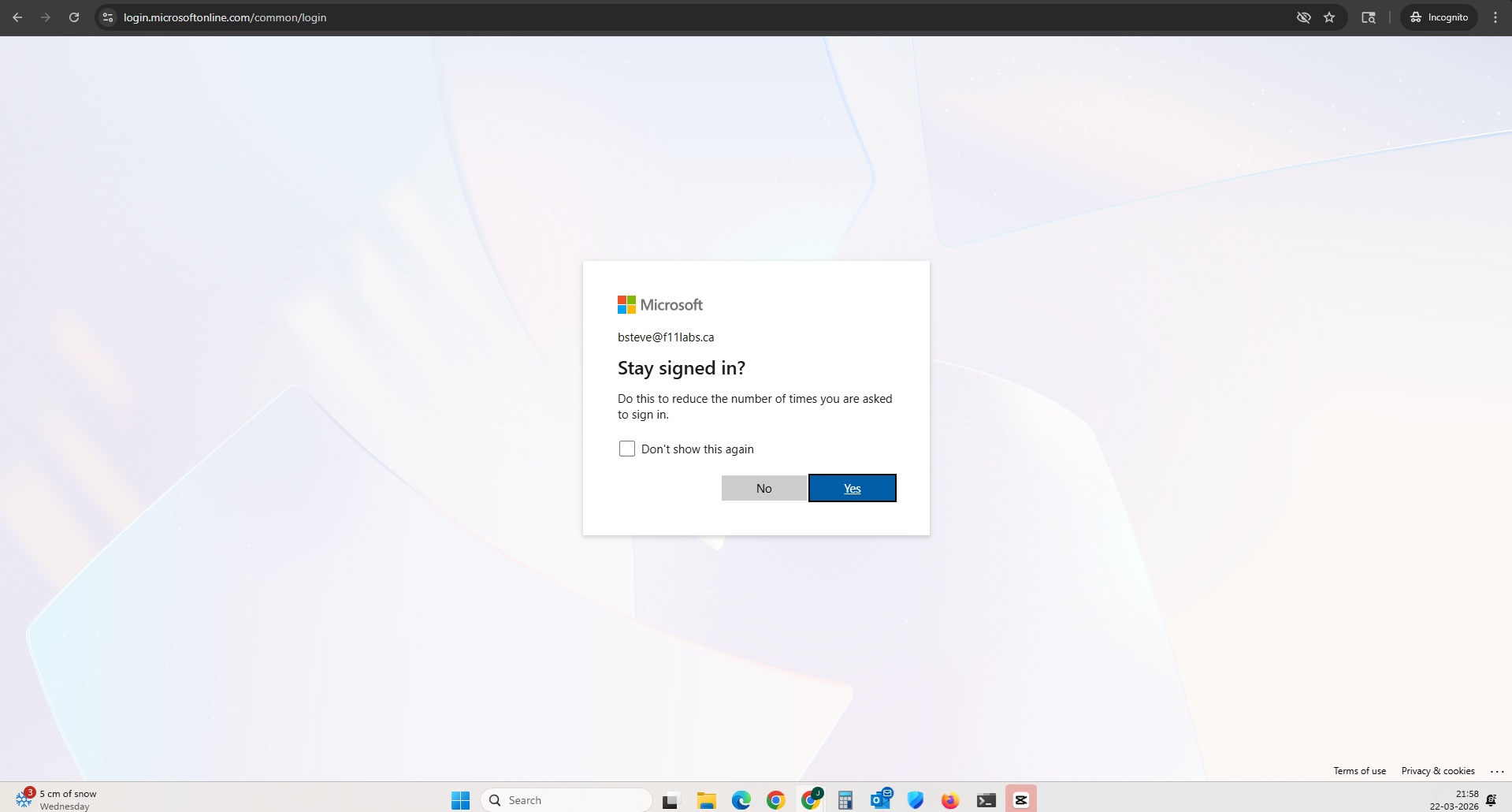
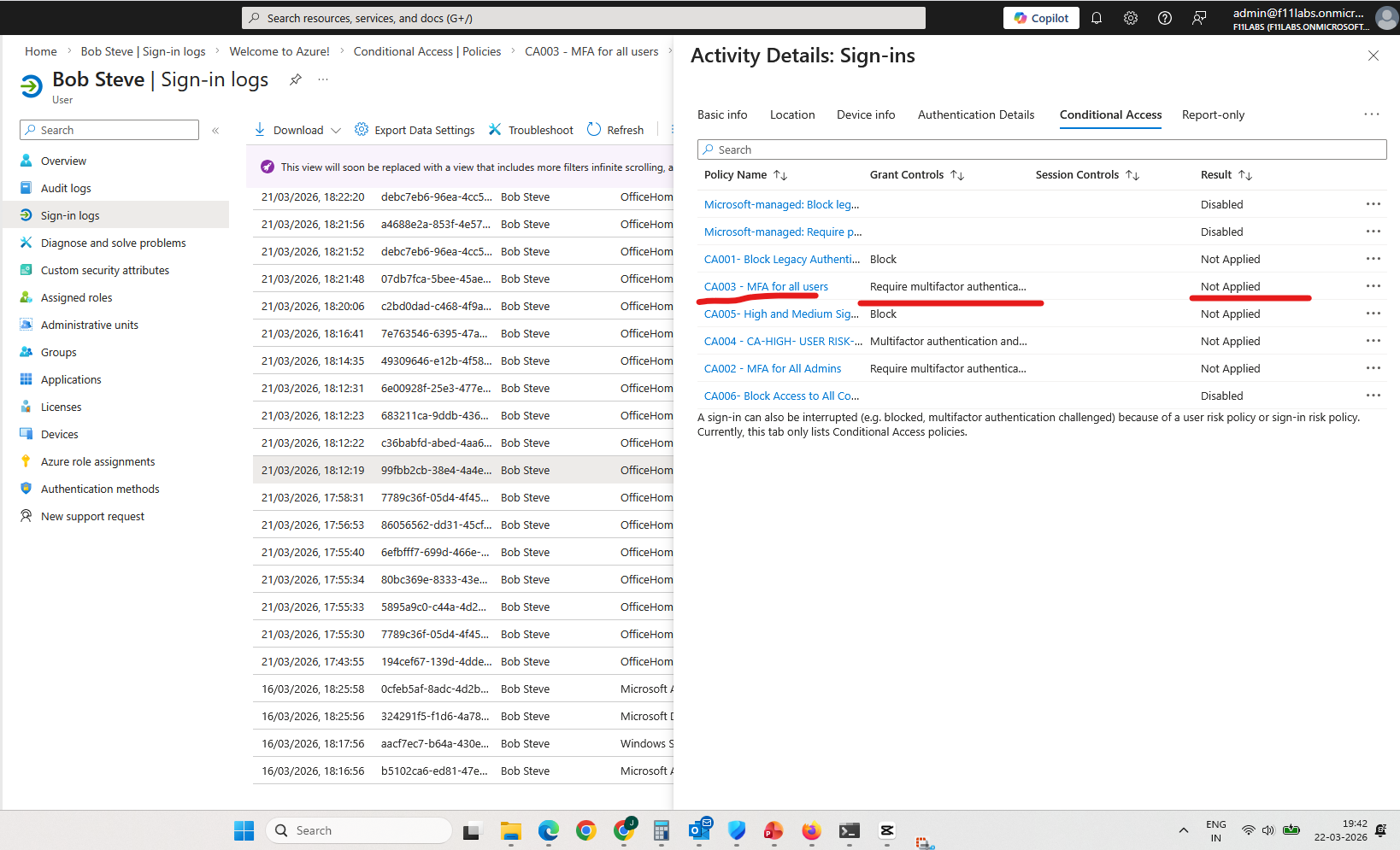
Evidence EID-EXP-010-04
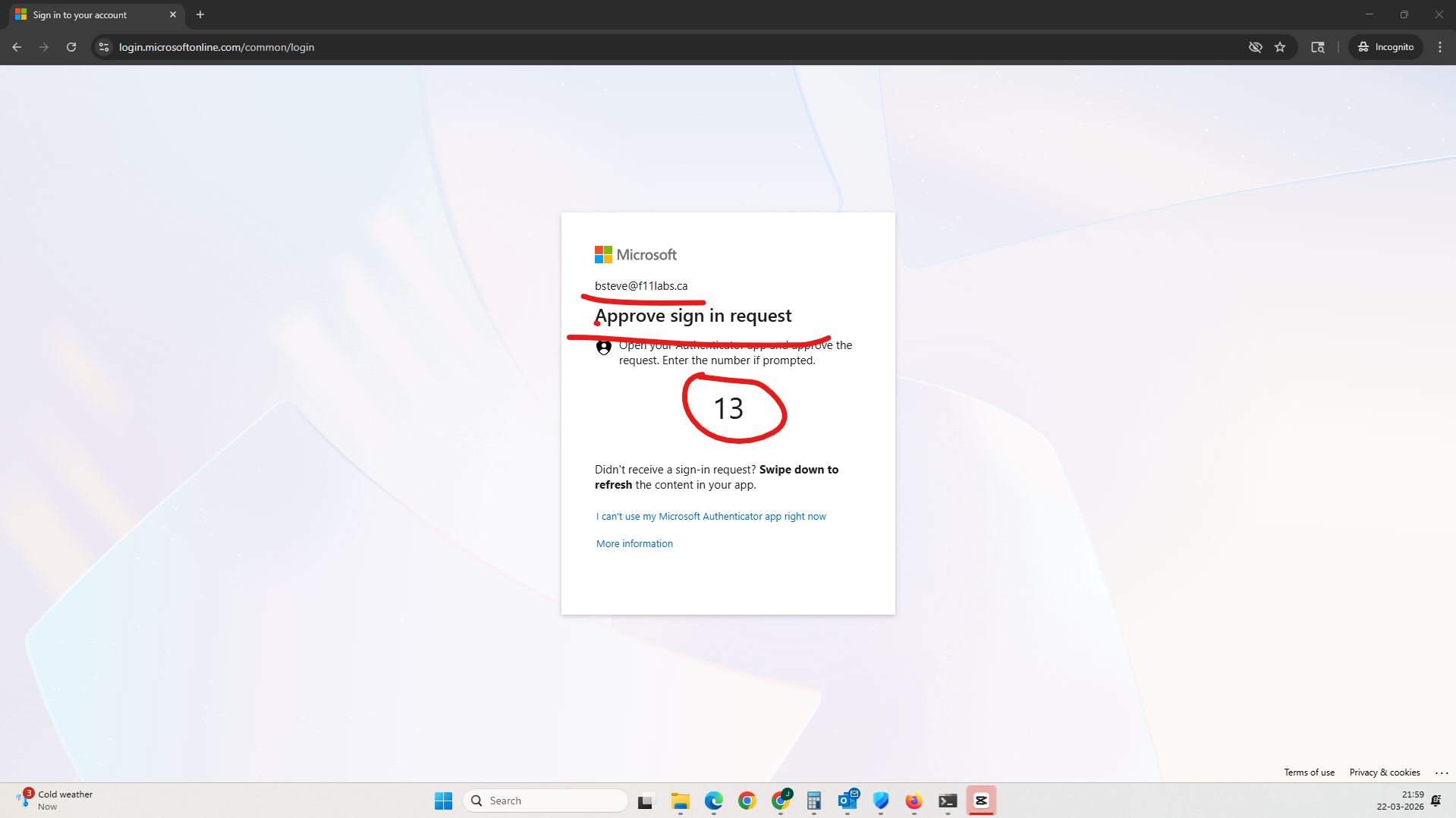
Control Area: Authentication – External Location
Observation: User authentication from an external network triggers MFA.
Expected Secure State: MFA enforcement should not depend solely on location.
Actual Result: MFA is enforced only when authentication originates outside a trusted location.
Impact: Security enforcement is inconsistent and depends on context.
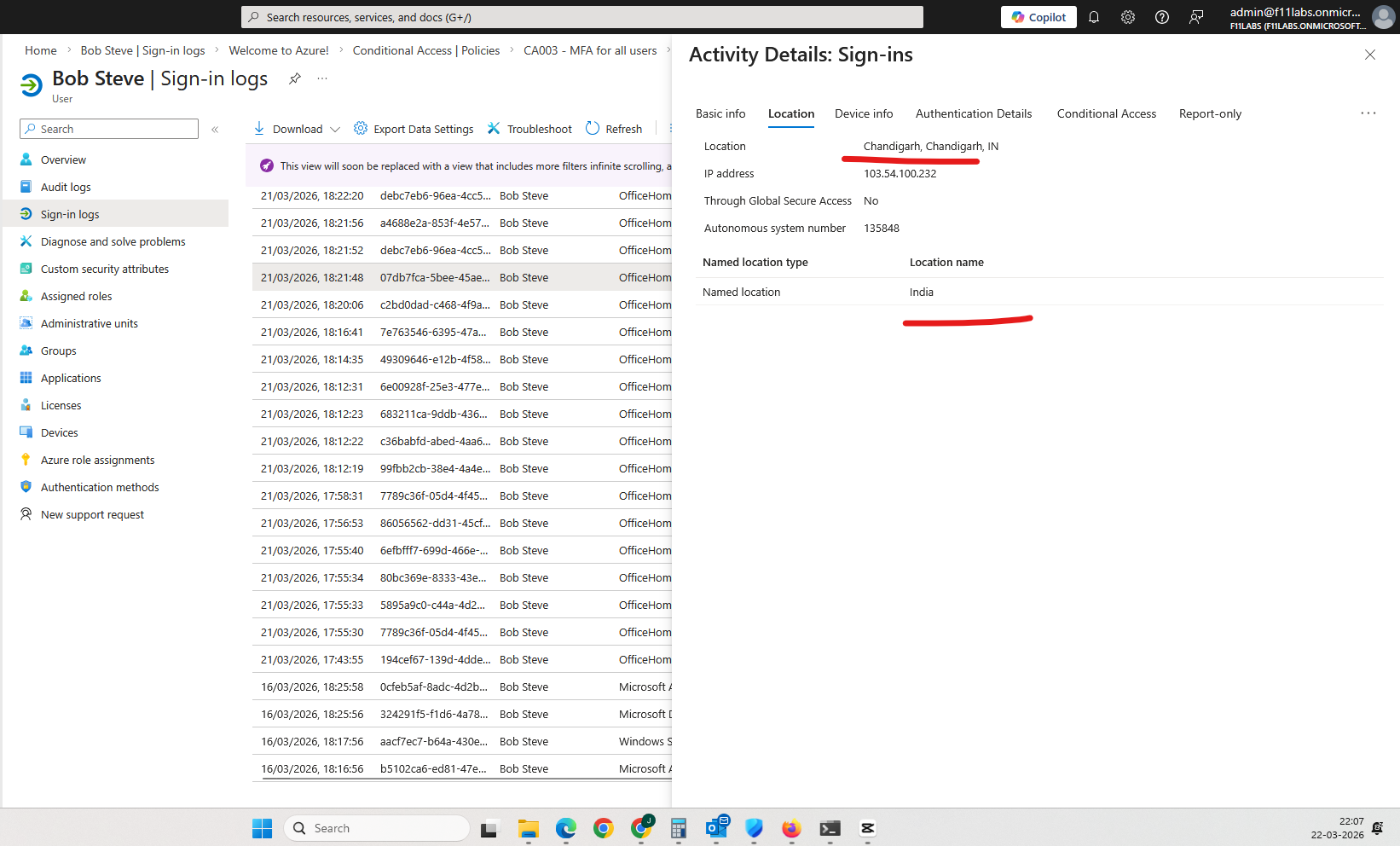
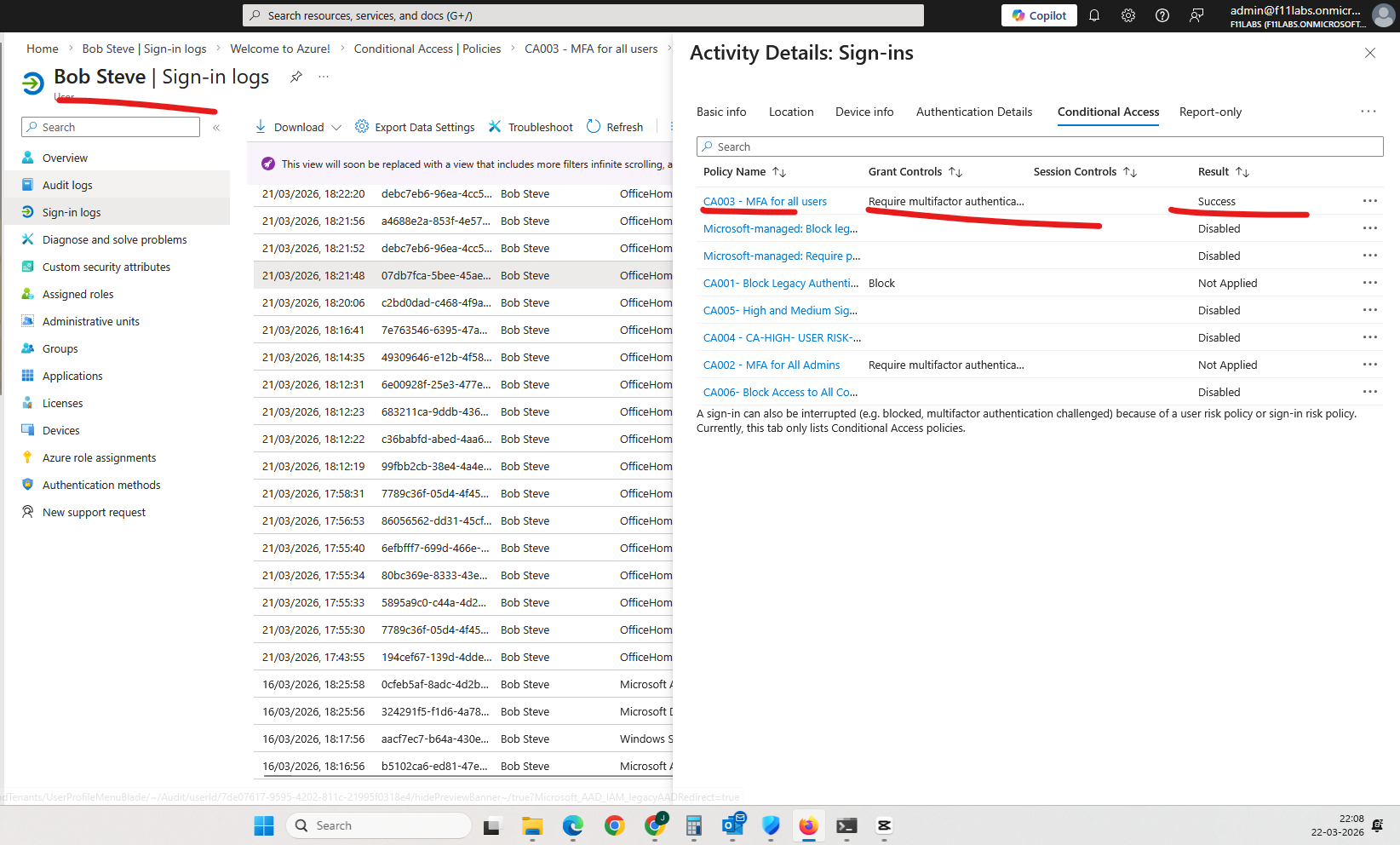
Evidence EID-EXP-010-05
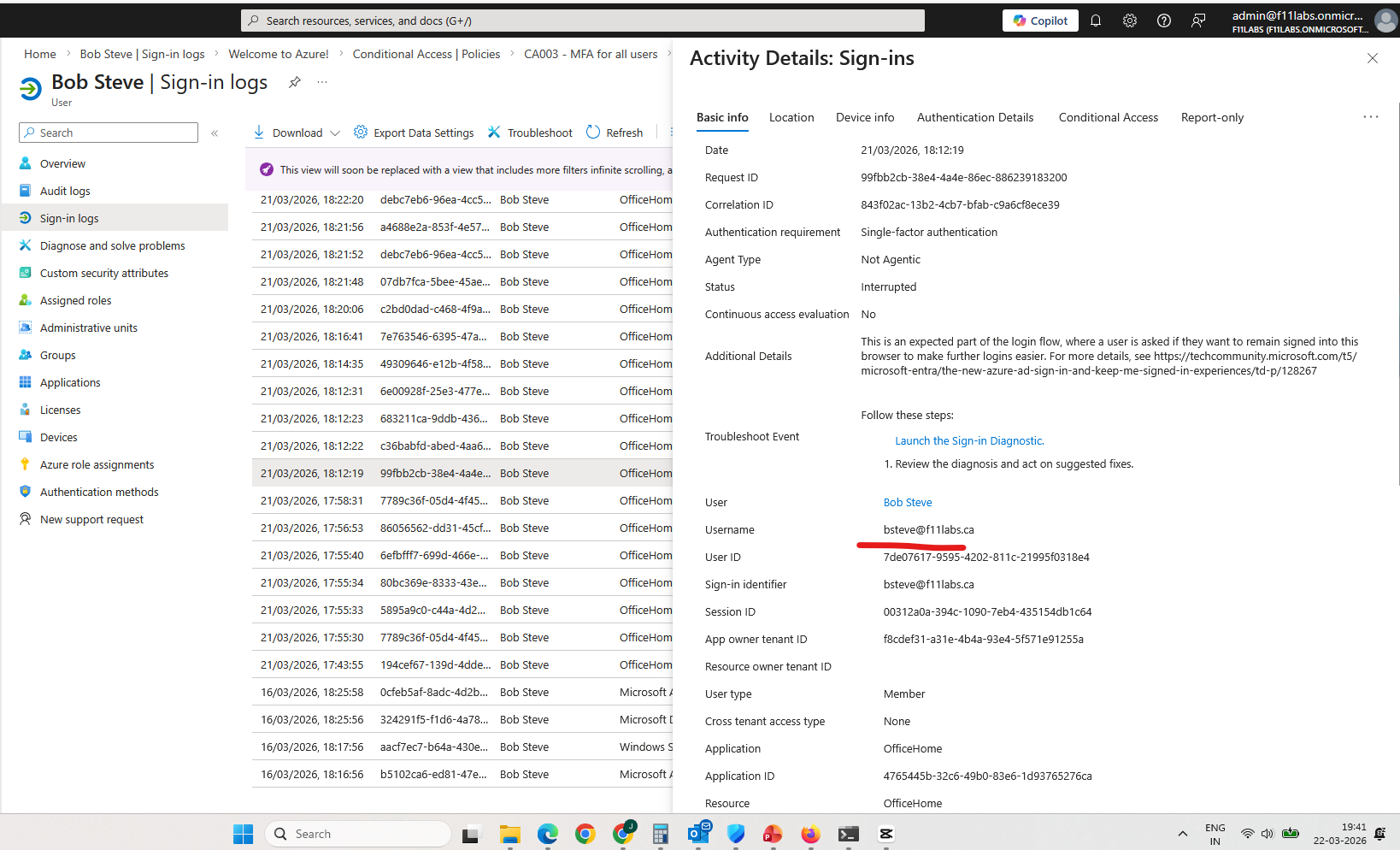
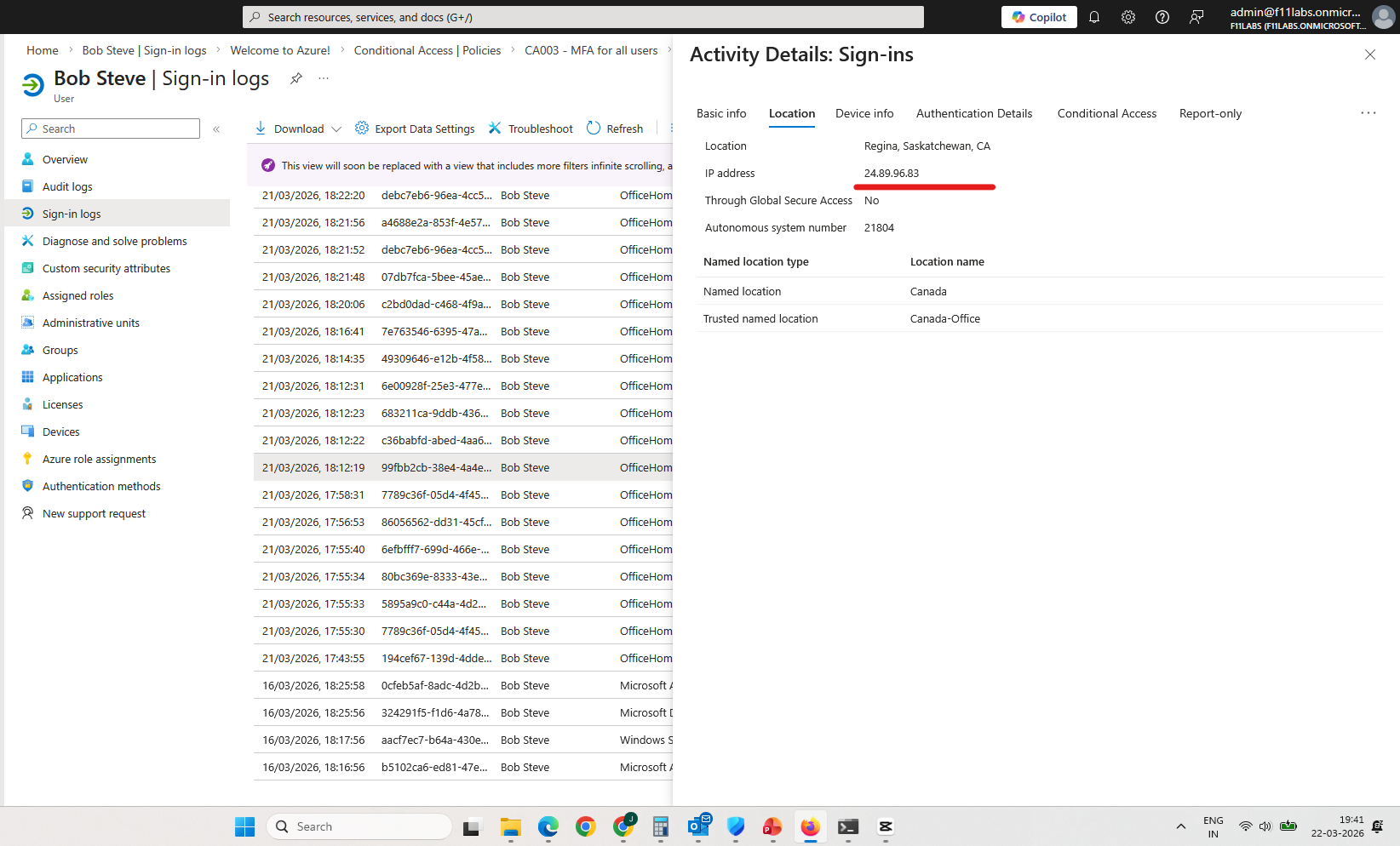
Control Area: Sign-In Logs / Conditional Access Evaluation
Observation: Sign-in logs show that Conditional Access decisions are based on location.
Expected Secure State: Authentication decisions should incorporate multiple security signals (device, risk, identity).
Actual Result: Conditional Access decisions are primarily influenced by location classification.
Impact: Location becomes the dominant factor in authentication decisions.
Evidence Artifact:
Evidence Summary
Evidence ID | Control Area | Result |
| 010-01 | Tenant Validation | Informational |
| 010-02 | Conditional Access Policy | Weak |
| 010-03 | Named Locations | Weak |
| 010-04 | Authentication (Trusted) | Weak |
010-05 | Authentication (External) | Partial |
010-06 | Sign-In Logs | Informational |
Evidence-Based Conclusion
The evidence confirms that Conditional Access policies using Named Locations introduce implicit trust based on network location.
Authentication controls are reduced when users sign in from trusted IP ranges, resulting in:
- Inconsistent MFA enforcement
- Location-dependent authentication behavior
- Reduced verification strength inside trusted environments
This demonstrates that Named Locations should not be considered a strong security boundary.
Next Experiment
EID-EXP-011 – Impossible Travel Detection vs VPN Behavior in Microsoft Entra ID