EID-EXP-013 – Evidence
Experiment ID: EID-EXP-013
Category: Identity Protection
Title: Impossible Travel Detection vs VPN Behavior in Microsoft Entra ID
Result: Inconsistent risk detection with VPN-based authentication
Risk Rating: 🔴 High
Evidence Scope
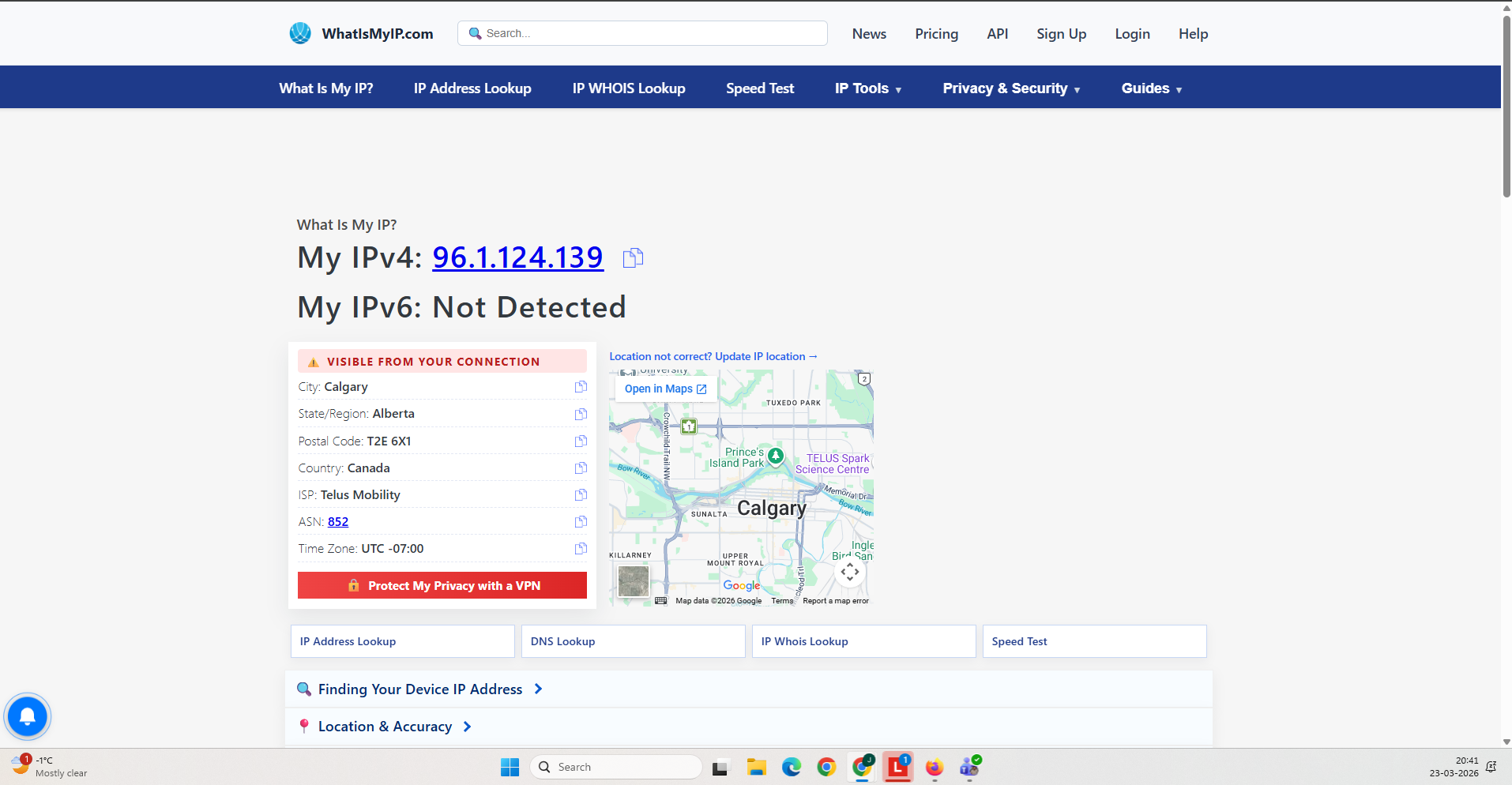
This evidence was collected from a hybrid identity environment using Microsoft Entra ID and Identity Protection.
Tenant Conditions:
- Microsoft Entra ID P2 license enabled
- Azure AD Connect configured (Password Hash Sync)
- Hybrid users synchronized from on-prem Active Directory
- No Conditional Access policies enforcing risk-based controls
- Identity Protection enabled with default configuration
- VPN services used to simulate geographically distributed sign-ins
This evidence demonstrates the behavior of Impossible Travel detection under standard conditions and with VPN infrastructure.
Tenant Validation 013-01
All evidence in this experiment was collected from the Microsoft Entra ID tenant.
F11labs with primary domain f11labs.onmicrosoft.com.Evidence Artifact:
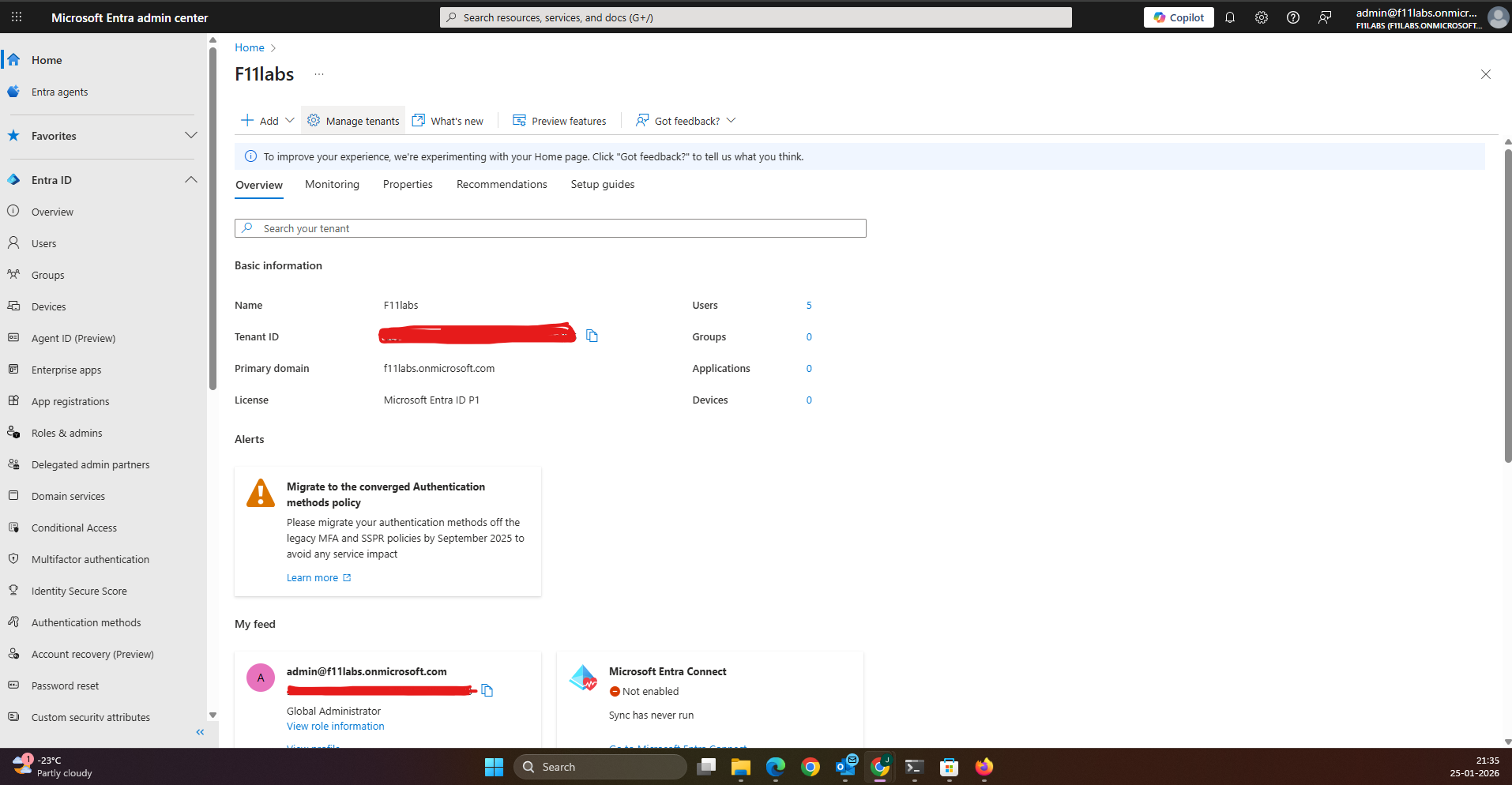
Evidence EID-EXP-013-01
Control Area: Identity Protection
Observation: Identity Protection is enabled, but user risk and sign-in risk policies are not enforced.
Expected Secure State: Risk-based policies should automatically enforce MFA or block access for risky sign-ins.
Actual Result: Risk detection is enabled, but automatic enforcement controls are not in place.
Impact: Risky sign-ins may be identified but remain unmitigated.
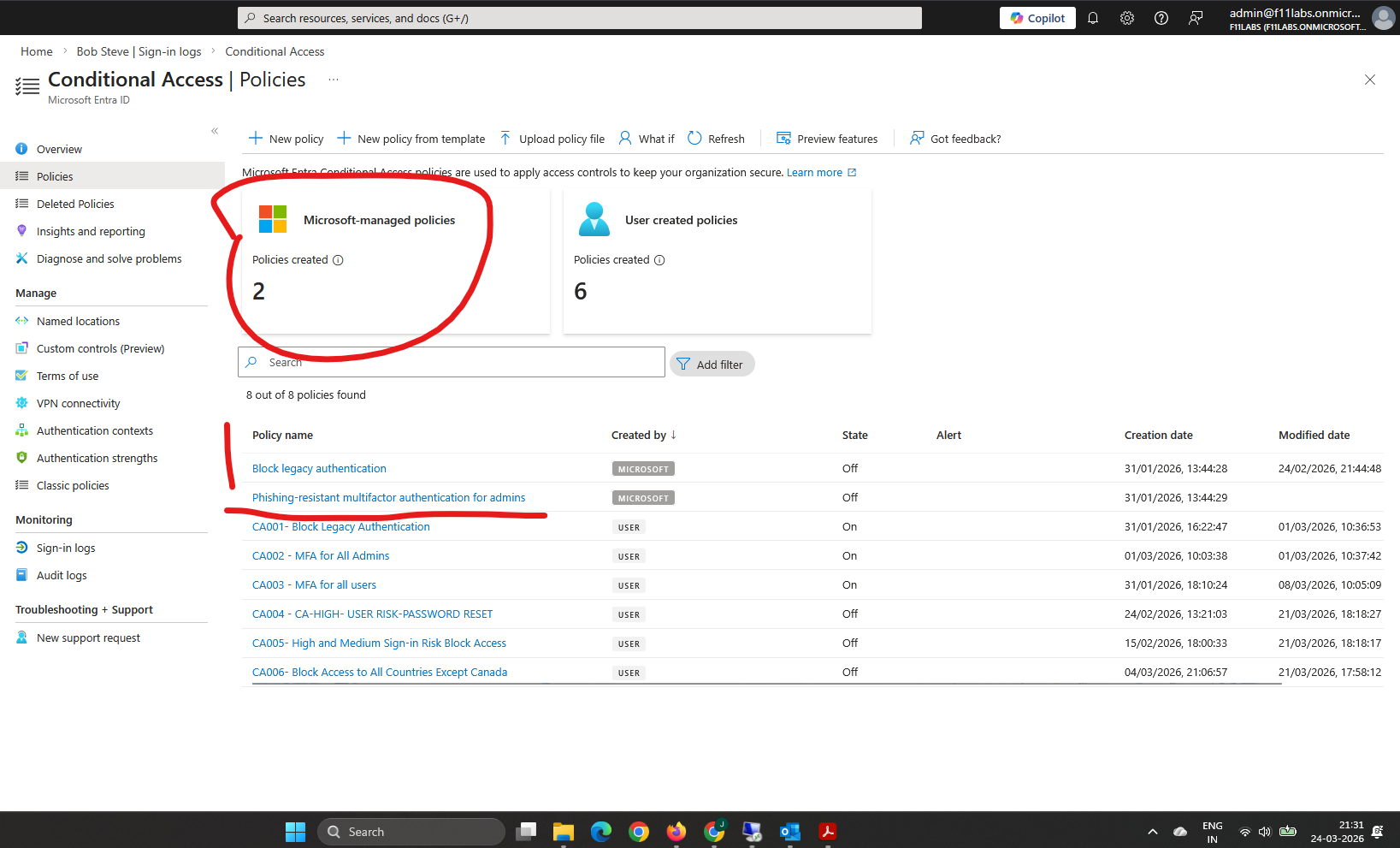
Evidence EID-EXP-013-02
Control Area: Baseline Authentication
Observation: A user signed in from a single geographic location without triggering risk signals.
Expected Secure State: Normal sign-in activity should not generate risk alerts.
Actual Result: No risk was detected for baseline authentication.
Impact: Establishes a baseline for authentication behavior.
Evidence EID-EXP-013-03
Control Area: Impossible Travel Detection
Observation: Two sign-ins occurred from geographically distant locations within a short timeframe.
Expected Secure State: The system should detect Impossible Travel and flag the sign-in as risky.
Actual Result: Impossible Travel detection was triggered, and the sign-in was flagged as risky.
Impact: Confirms Impossible Travel detection functions as expected under standard conditions.
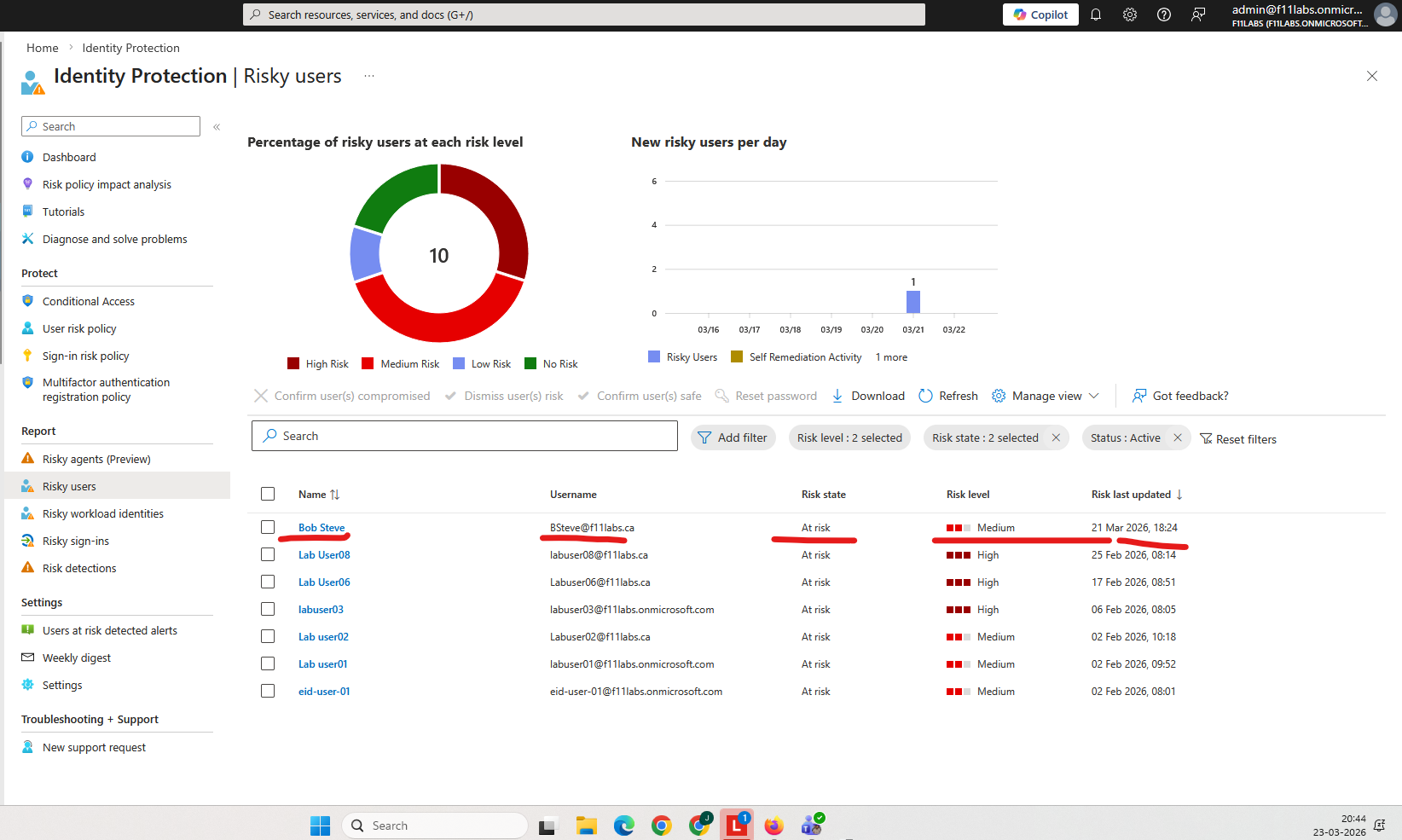
Evidence EID-EXP-013-04
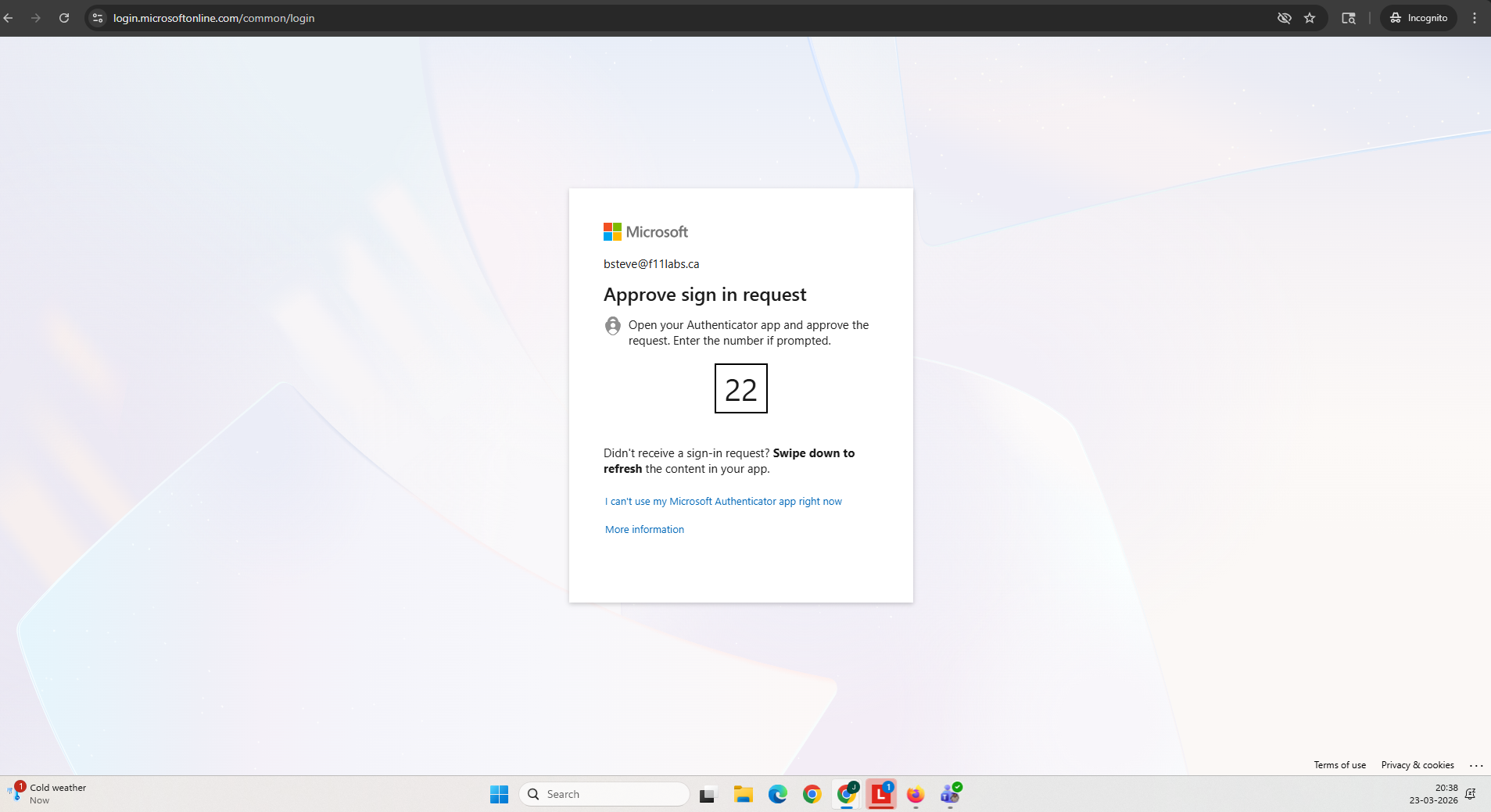
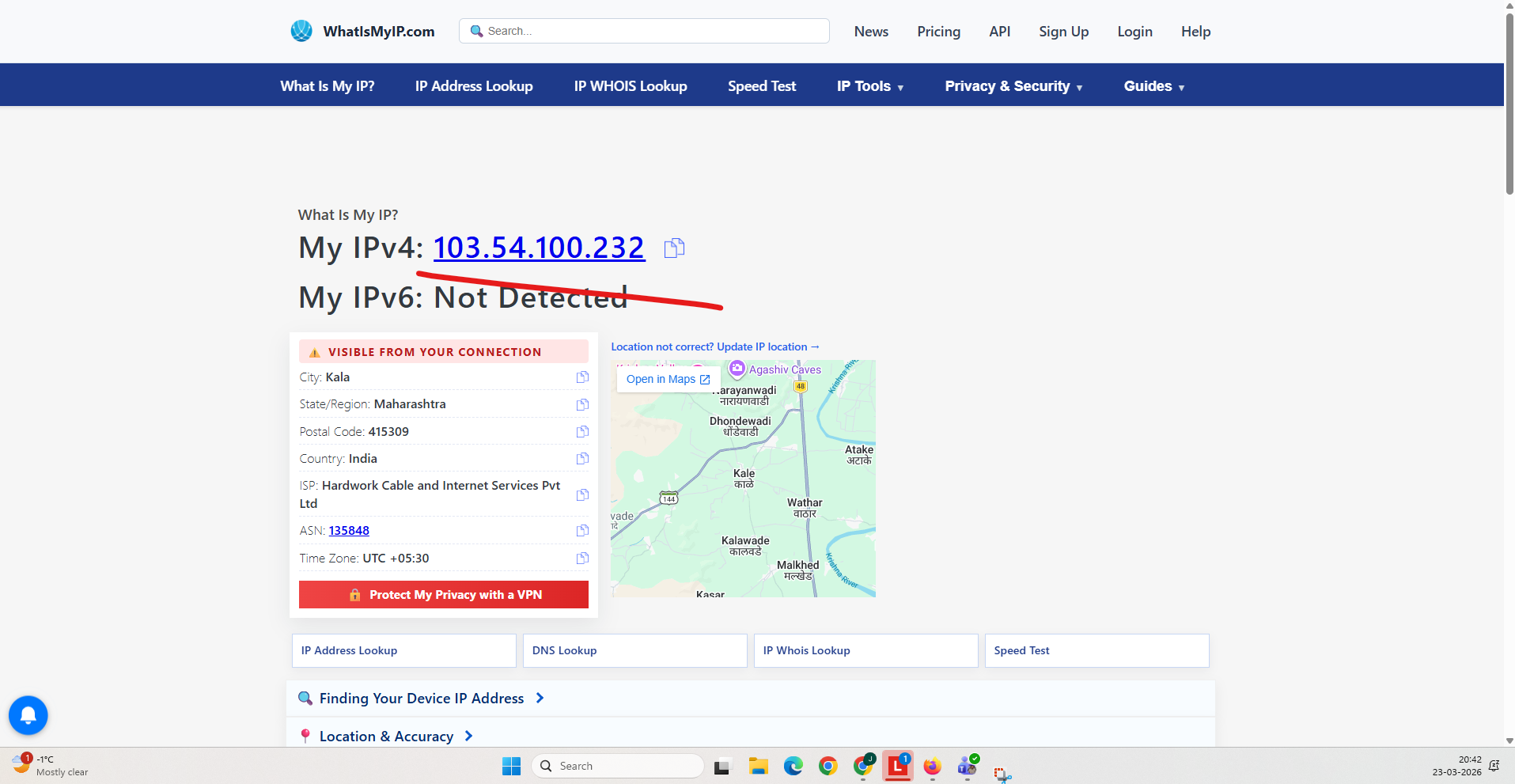
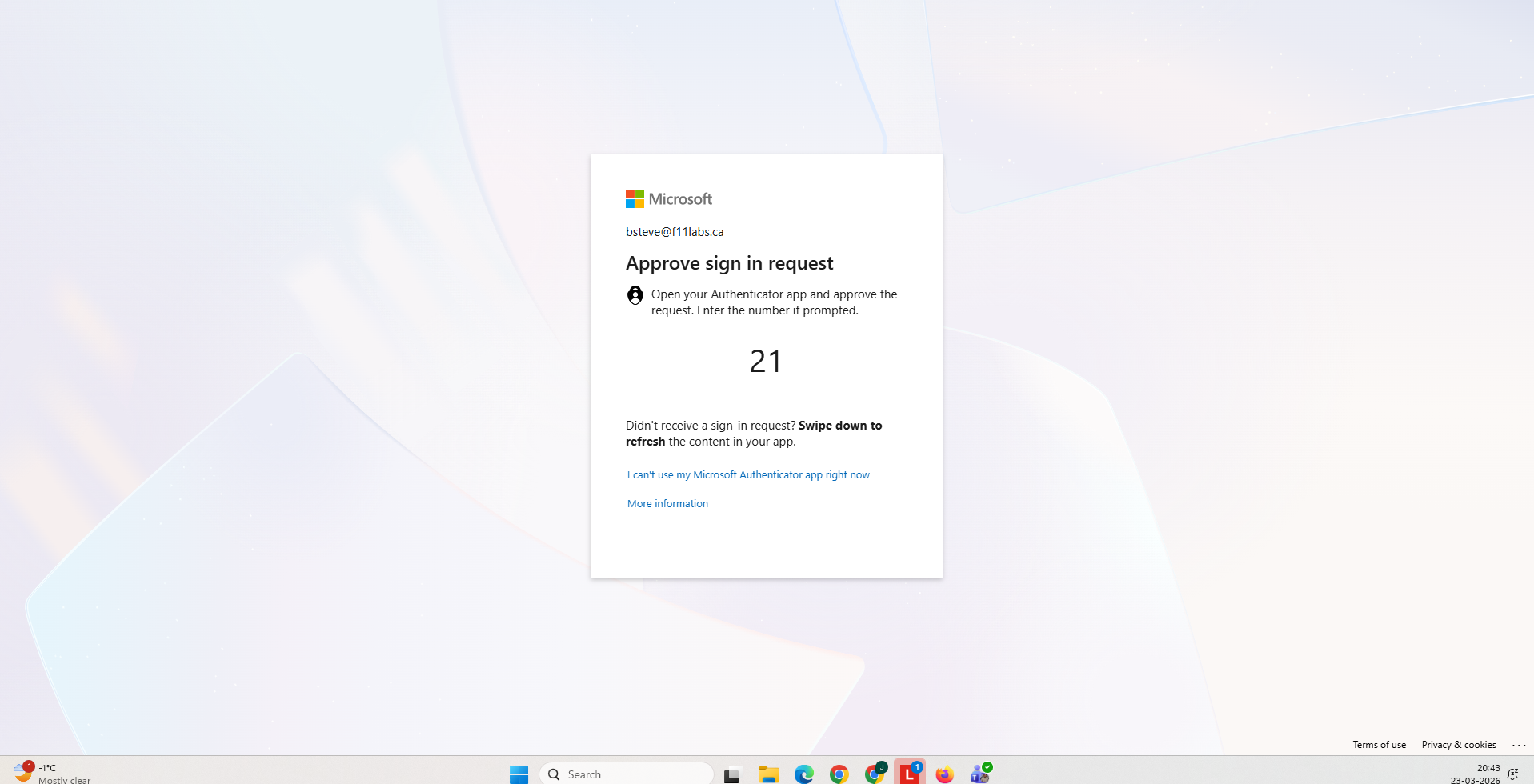
Control Area: VPN-Based Authentication
Observation: User authentication occurred via VPN endpoints across multiple geographic regions.
Expected Secure State: Rapid geographic changes through VPN should trigger Impossible Travel detection.
Actual Result: VPN-based sign-ins were not consistently flagged as Impossible Travel.
Impact: VPN infrastructure reduces the reliability of location-based anomaly detection.
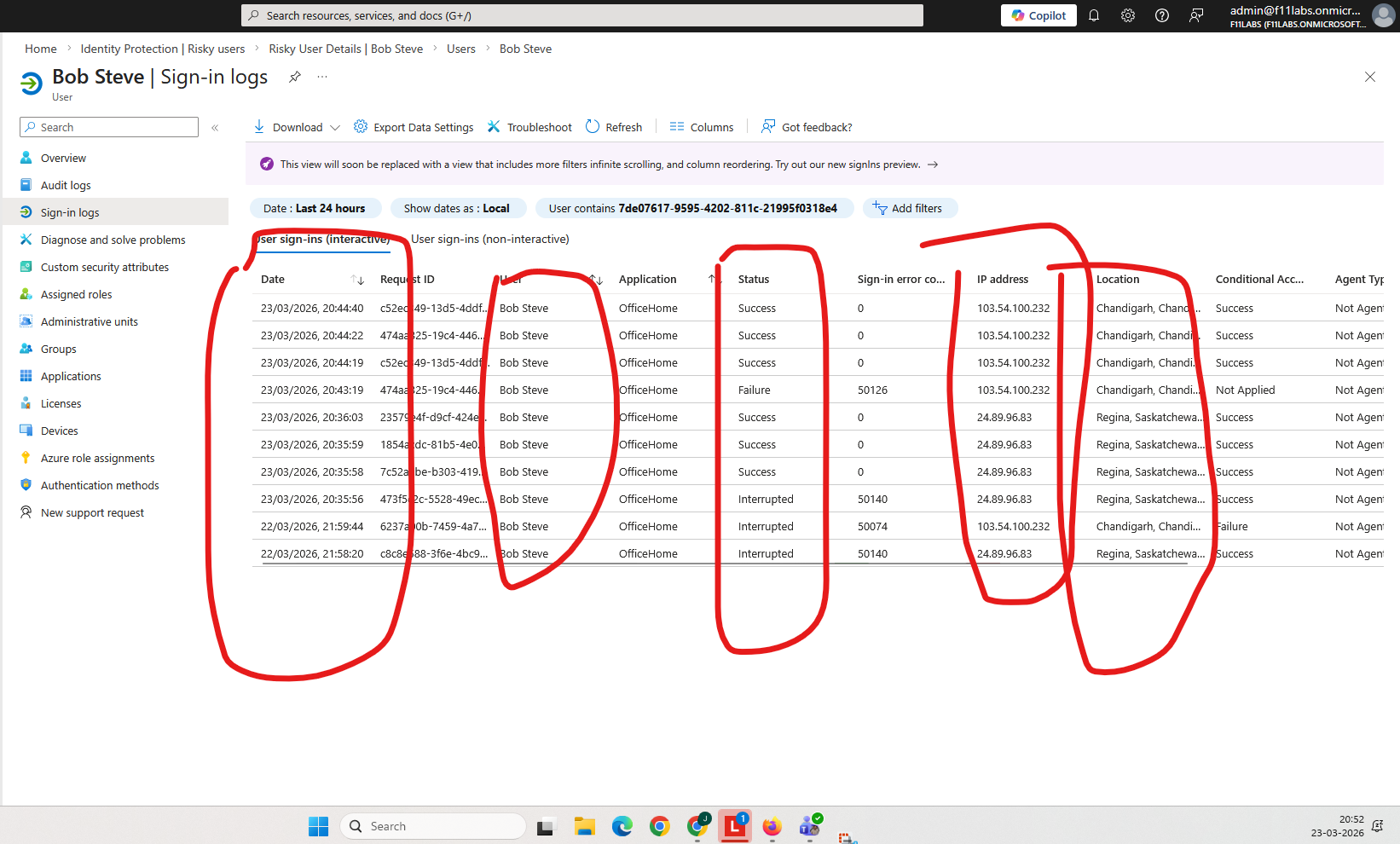
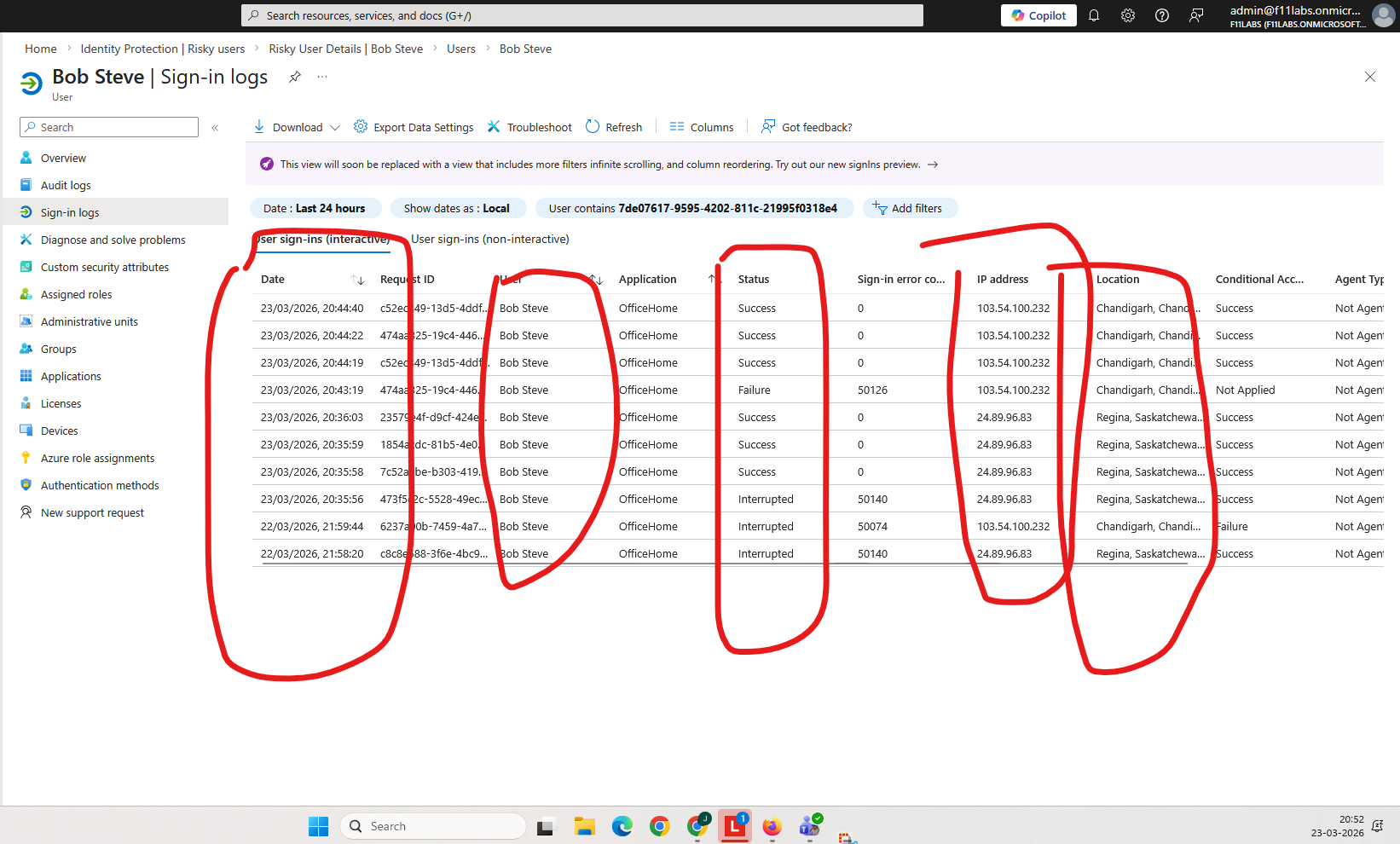
Evidence EID-EXP-013-05
Control Area: Sign-In Logs
Observation: Sign-in logs display varying risk levels based on IP address and geographic source.
Expected Secure State: Risk evaluation should consistently identify anomalous behavior across locations.
Actual Result: Risk detection varies based on IP reputation and signal confidence
Impact: Authentication risk scoring is influenced by external factors beyond location changes.
Evidence Summary
| 013-01 | Tenant Validation | Informational |
| 013-02 | Identity Protection | Partial |
| 013-03 | Baseline Authentication | Informational |
| 013-04 | Impossible Travel Detection | Effective |
| 013-05 | VPN Behavior | Weak |
| 013-06 | Sign-In Logs | Partial |
Evidence-Based Conclusion
The evidence confirms that Microsoft Entra ID can detect Impossible Travel under standard authentication scenarios.
However, when VPN infrastructure is introduced:
- Detection becomes inconsistent.
- Some anomalous sign-ins are not flagged.
- Risk evaluation depends on IP reputation and signal confidence.
This demonstrates that Impossible Travel detection is not a guaranteed control and should not be relied on as a primary security mechanism.
Next Experiment
EID-EXP-014 – Legacy Authentication Bypass and Detection in Hybrid Identity