EID-EXP-014 – MFA Fatigue Attack Simulation – Push Notification Abuse in Microsoft Entra ID
Experiment ID: EID-EXP-014
Category: Authentication / MFA
Title: MFA Fatigue Attack Simulation – Push Notification Abuse in Microsoft Entra ID
Result: Repeated MFA push notifications may cause users to approve unintended authentication requests.
Risk Rating: High
Evidence Scope
This experiment assesses Microsoft Entra ID MFA's response to repeated authentication attempts that generate multiple push notifications in an MFA fatigue scenario.
MFA fatigue attacks exploit user behavior by increasing the chance of accidental or coerced approval through repeated MFA prompts, rather than technical vulnerabilities.
The objective is to determine whether:
- Multiple MFA prompts can be triggered.
- A single approval grants full access
- Any detection or enforcement mechanisms prevent misuse.
Tenant Conditions:
- Microsoft Entra ID tenant with MFA enabled
- Microsoft Authenticator is configured with push notifications.
- No number matching is enforced.
- No Conditional Access policies limiting MFA attempts
- One standard test user
- Hybrid identity environment (Azure AD Connect – Password Hash Sync)
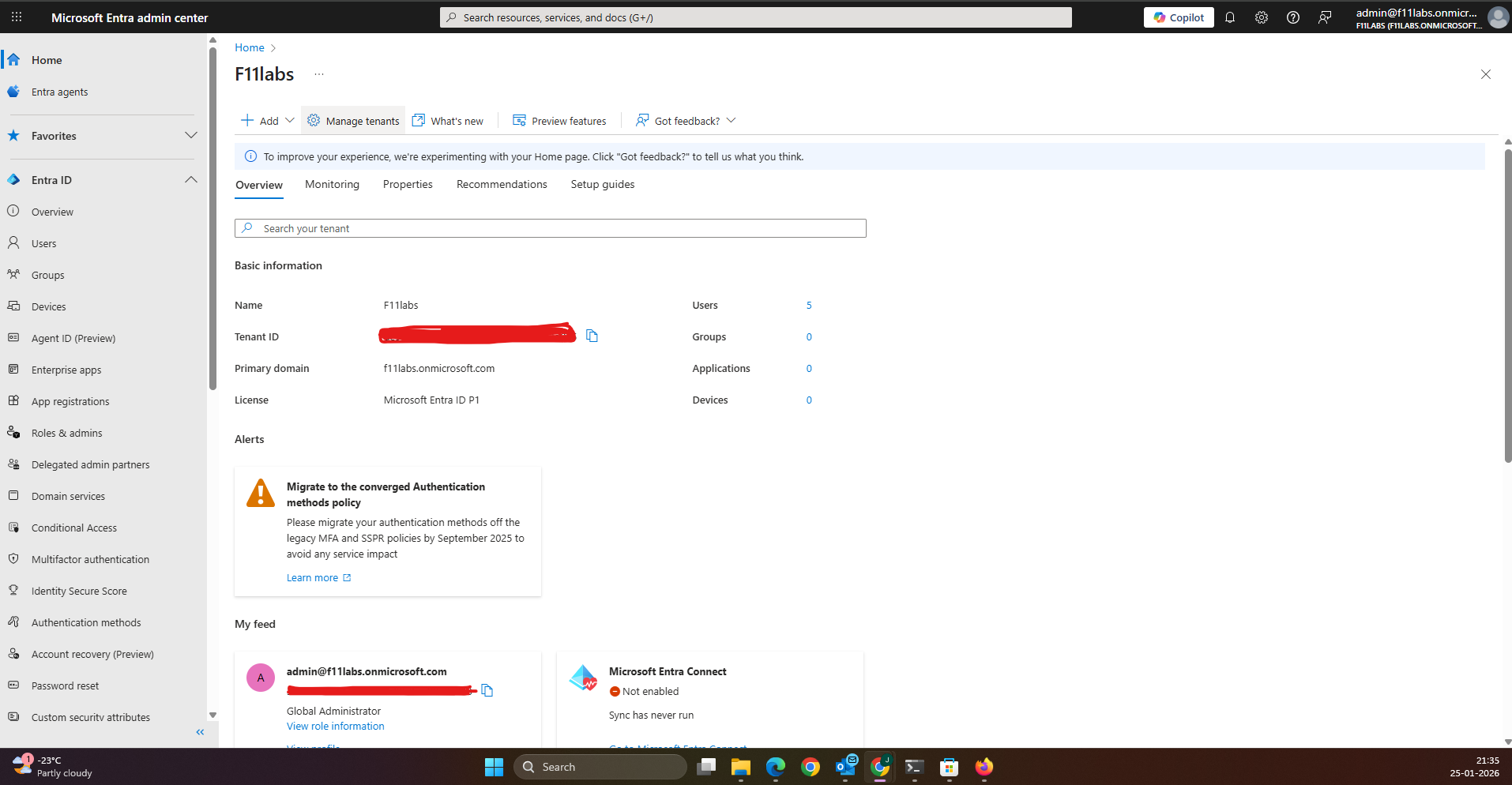
Tenant Validation 014-01
All evidence in this experiment was collected from the Microsoft Entra ID tenant.
F11labs with primary domain f11labs.onmicrosoft.com.
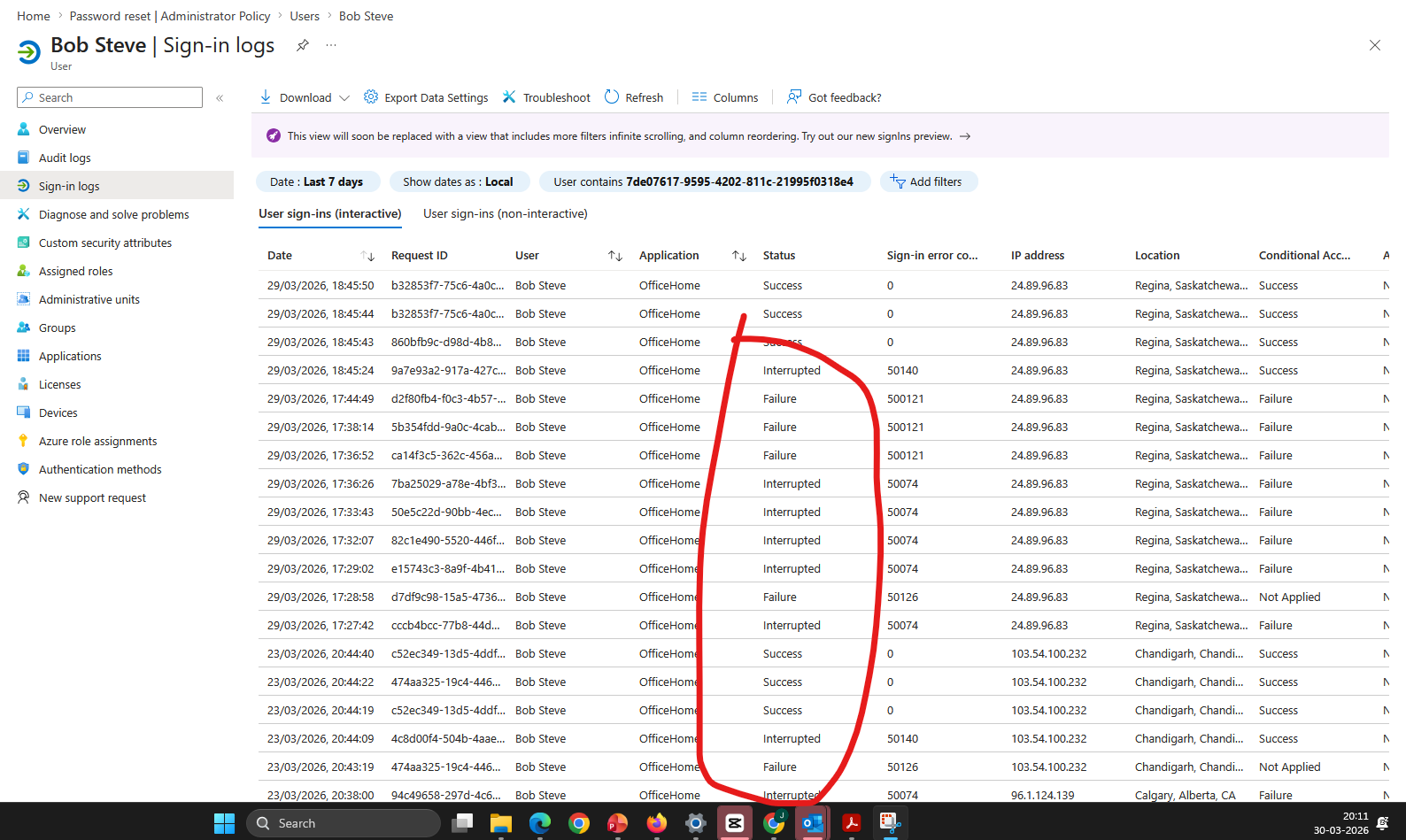
EID-EXP-014-02 – Multiple MFA Prompts Can Be Triggered
Control Area: Authentication – MFA Prompt Behavior
Observation: Repeated login attempts generate multiple MFA push notifications on the user’s device.
Expected Secure State: Repeated MFA requests should be rate-limited or identified as suspicious.
Actual Result: Multiple MFA push notifications are delivered without restriction.
Each authentication attempt generates a new prompt.
Impact: Attackers can induce MFA fatigue by overwhelming users with repeated prompts.
This increases the likelihood of accidental approval.
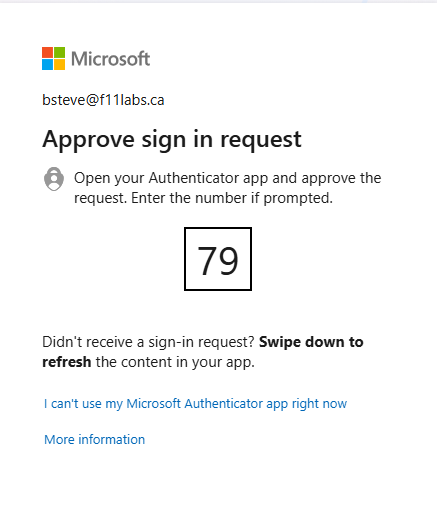
EID-EXP-014-03 – MFA Approval Grants Immediate Access
Control Area: Authentication – MFA Validation
Observation: A single approval of an MFA push notification completes authentication.
Expected Secure State: Suspicious authentication patterns should be further validated or denied access.
Actual Result: User approves one MFA request.
Authentication is granted immediately.
Impact: A single user action is sufficient to grant access, even after multiple suspicious prompts.
Authentication success is based on approval, not context.
EID-EXP-014-04 – Authentication Session Established
Control Area: Authentication Outcome
Observation: After MFA approval, the session is established successfully.
Expected Secure State: Suspicious login behavior should trigger additional controls or session restrictions.
Actual Result: Access is granted after MFA approval.
The session is established without further verification.
Impact: Attackers gain full access once MFA is approved.
No additional safeguards are applied post-authentication.
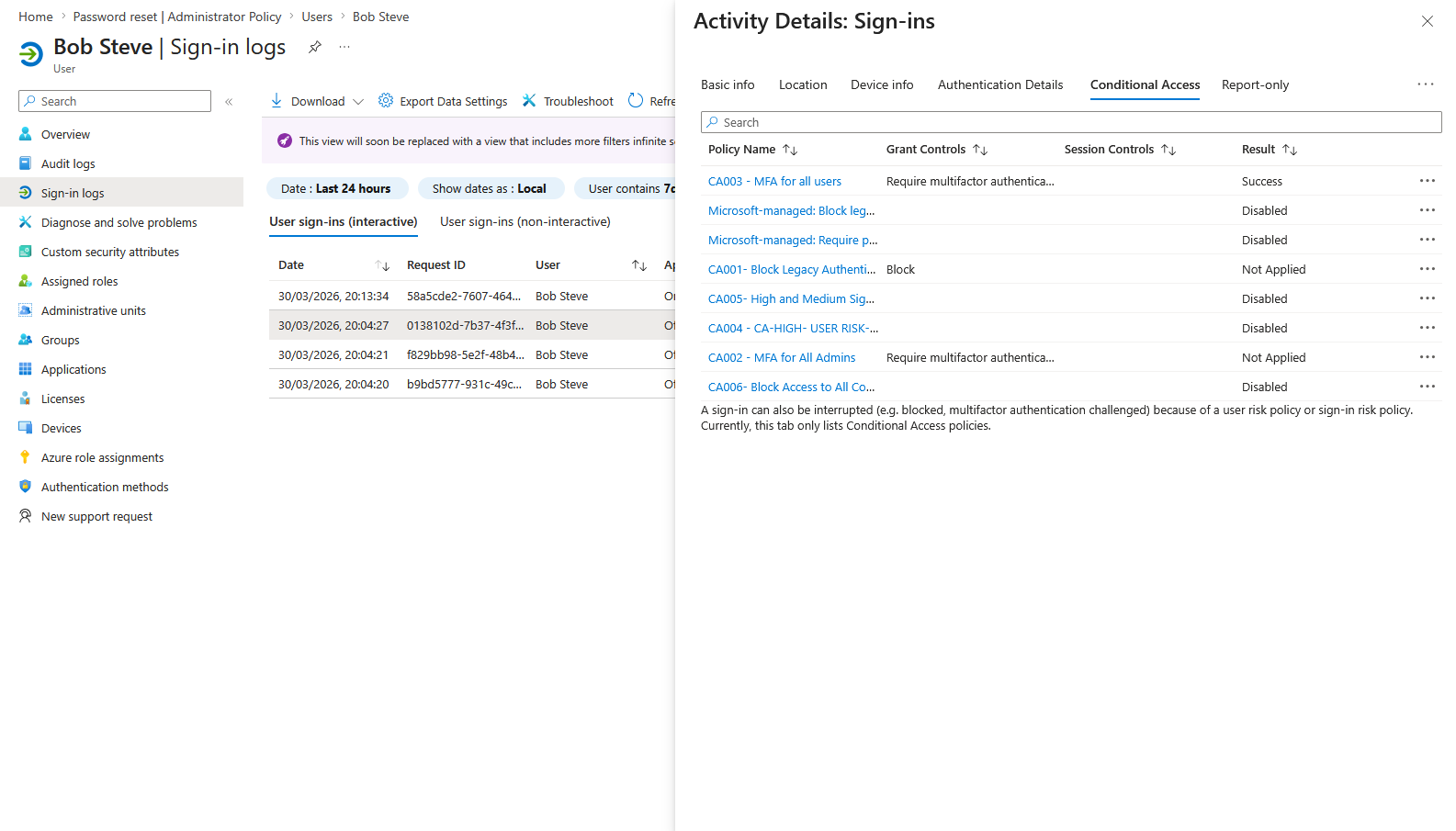
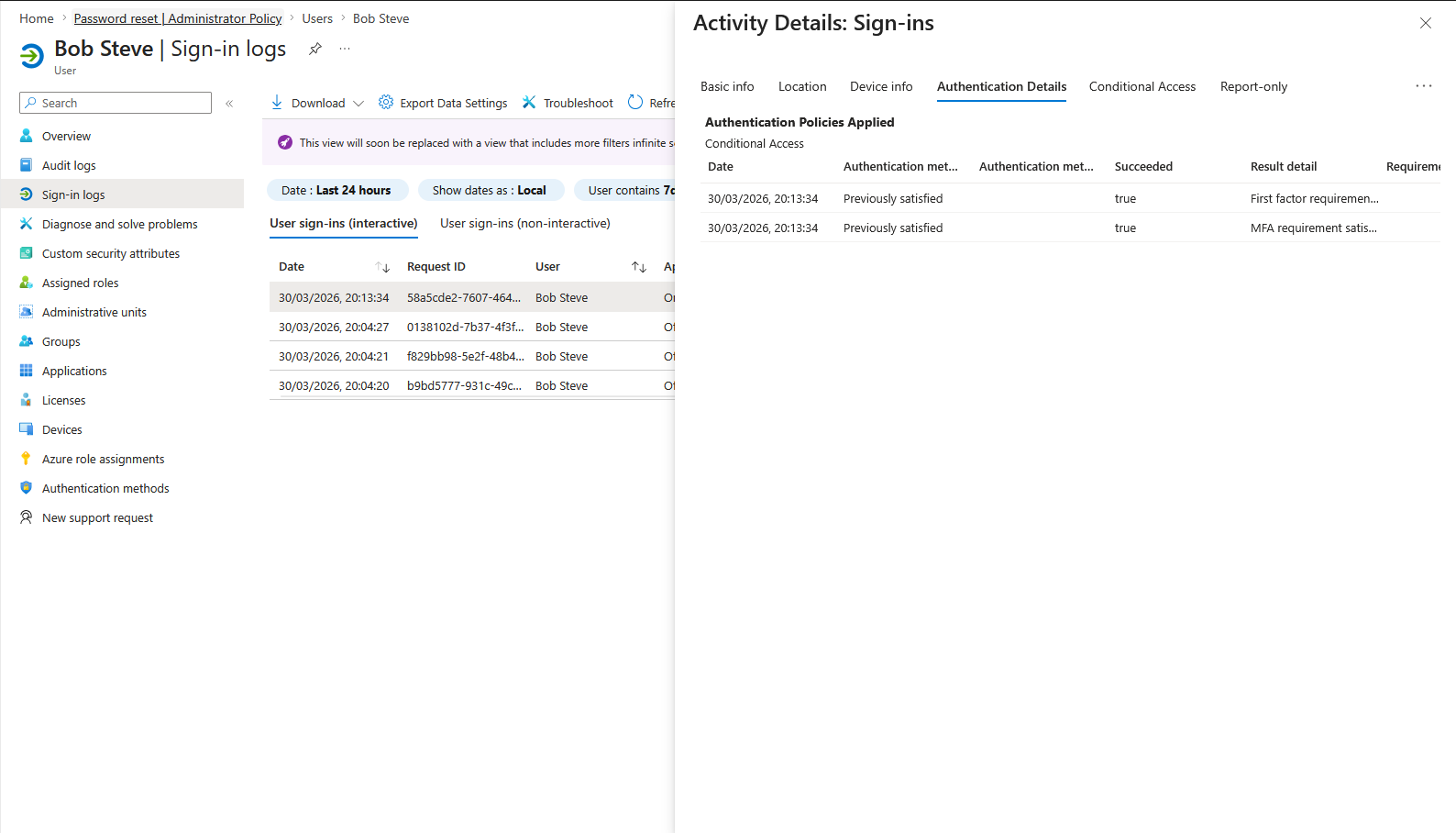
EID-EXP-014-05 – Sign-In Logs Show MFA as Satisfied
Control Area: Monitoring – Sign-In Logs
Observation: Sign-in logs indicate successful completion of MFA.
Expected Secure State: Suspicious MFA patterns should generate alerts or elevated risk levels.
Actual Result: MFA is marked as “Satisfied” in sign-in logs.
There is no indication of abnormal MFA activity.
Impact: Limited visibility into MFA fatigue scenarios.
Administrators cannot easily distinguish between legitimate and coerced approvals.
Evidence Summary
| 015-01 | Tenant Validation | Informational |
| 015-02 | MFA Prompt Behavior | High – Unrestricted prompts |
| 015-03 | MFA Approval | High – Single approval grants access |
| 015-04 | Authentication Outcome | High – Full access granted |
| 015-05 | Sign-In Logs | Informational – No anomaly indication |
Evidence-Based Conclusion
This experiment confirms that MFA fatigue attacks exploit user behavior rather than system vulnerabilities. Microsoft Entra ID:
- Allows repeated MFA prompts
- Accepts a single approval as valid authentication
- Does not differentiate between legitimate and coerced approvals
As a result:
MFA alone is insufficient if user interaction can be manipulated.