EID-EXP-016 – Evidence: OAuth Consent Phishing (No Password, No MFA Attack)
Experiment ID: EID-EXP-016
Category: Identity / OAuth Abuse / Token-Based Access
Title: OAuth Consent Phishing Leading to Unauthoriszed Access Without Credential Theft
Result: Users may grant persistent access to malicious applications without compromising passwords or bypassing MFA.
Risk Rating: Critical
Tenant Conditions / Settings (Baseline)
- Microsoft Entra ID, which is Microsoft's cloud-based identity and access management service, is configured with default security settings.
- MFA enabled for all users
- Conditional Access policies enforced
- User consent for applications enabled (default state)
- No admin approval workflow configured
- No monitoring for application consent events
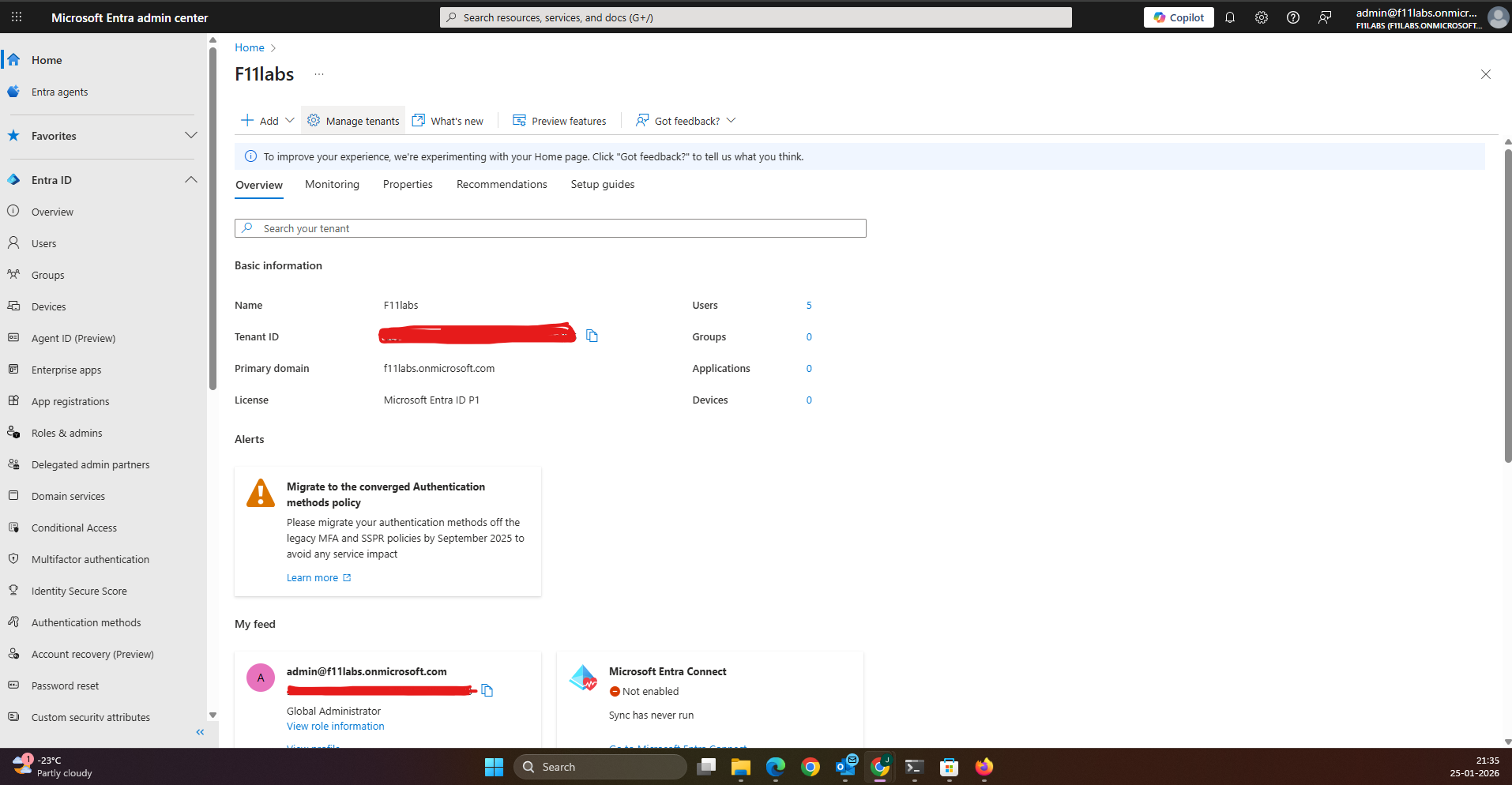
Tenant Validation 016-01
All evidence in this experiment was collected from the Microsoft Entra ID tenant F11labs with primary domain f11labs.onmicrosoft.com.
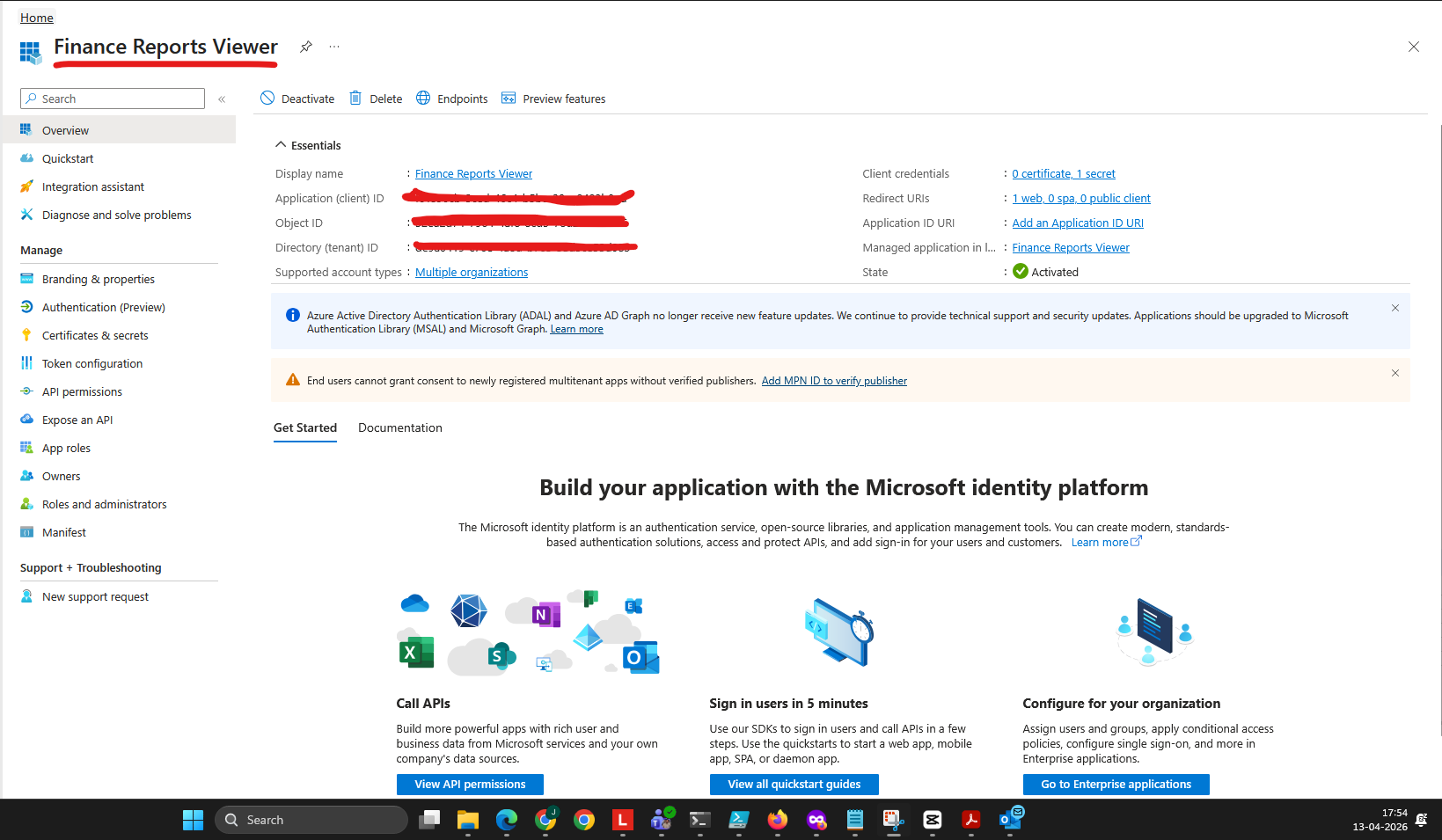
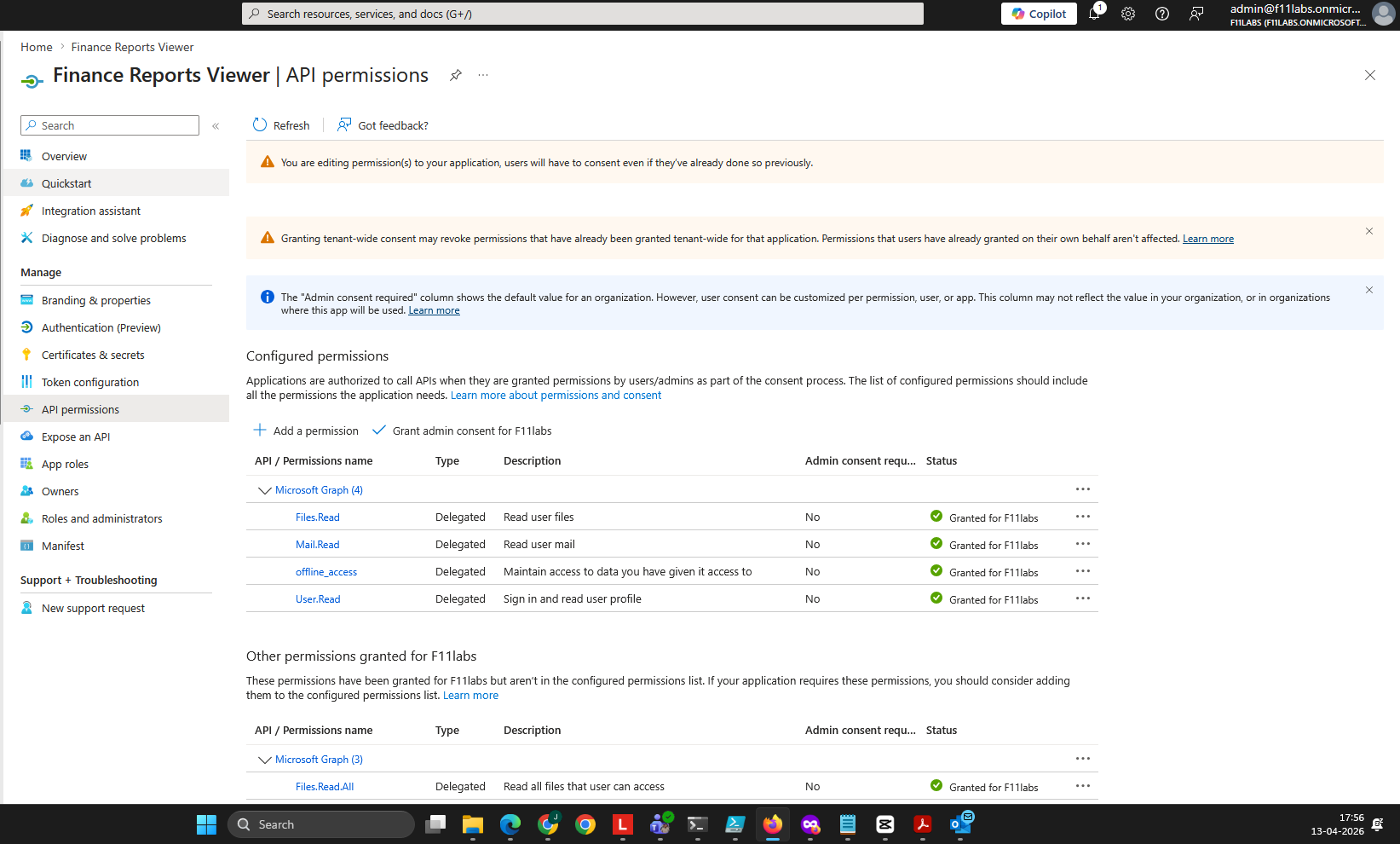
Evidence EID-EXP-016-02 – Malicious Application Registration and Permission Abuse
Control Area: Application Registration / API Permissions
Observation:
A malicious application was registered with delegated Microsoft Graph API permissions, which allow it to act on behalf of a user and access data, such as:
- Mail.Read
- Files.Read
- User.Read
- offline_access
The application name was crafted to appear legitimate, for example, “Finance Reports Viewer.”
Expected Secure State:
- Application registrations should be restricted or monitored.
- High-risk permissions should require admin approval.
- Application naming and publisher verification should be validated.
Actual Result:
The application was registered and configured with sensitive permissions without restrictions or alerts.
Impact:
- Attackers can access sensitive data by abusing user-granted permissions to legitimate-looking applications without immediate detection.
- Users are more likely to trust and grant applications access with legitimate-sounding names, increasing the risk.
- Such application creation is not detected immediately, allowing unauthorized access to persist.
Evidence Artifacts
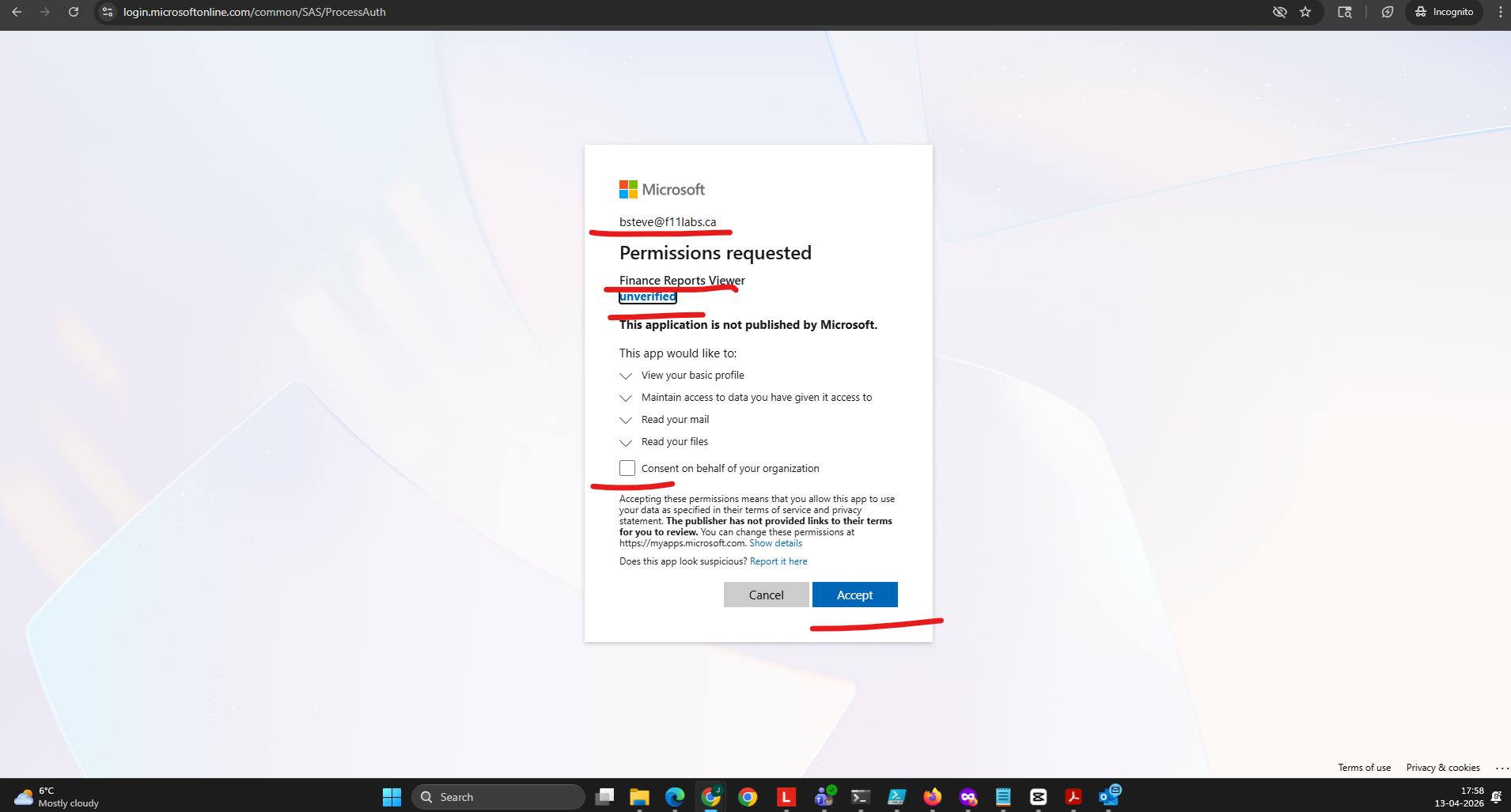
Evidence EID-EXP-016-03 – User Consent Grant via Phishing Link
Control Area: User Consent / Authorization Flow
Observation: A consent URL was generated and sent to a targeted user.
The user:
- Logged in successfully
- Completed MFA
- Approved the requested permissions
Expected Secure State:
- Users should not be allowed to consent to high-risk permissions.
- Admin approval workflow should be enforced.
- Users should be educated or blocked from granting access.
Actual Result:
User consent was granted without warnings or restrictions.
Impact:
- The legitimate authentication flow is exploited.
- No credential theft required
- No MFA bypass required
- Access is obtained through trusted authorization.
Evidence Artifacts
Authorization request URL
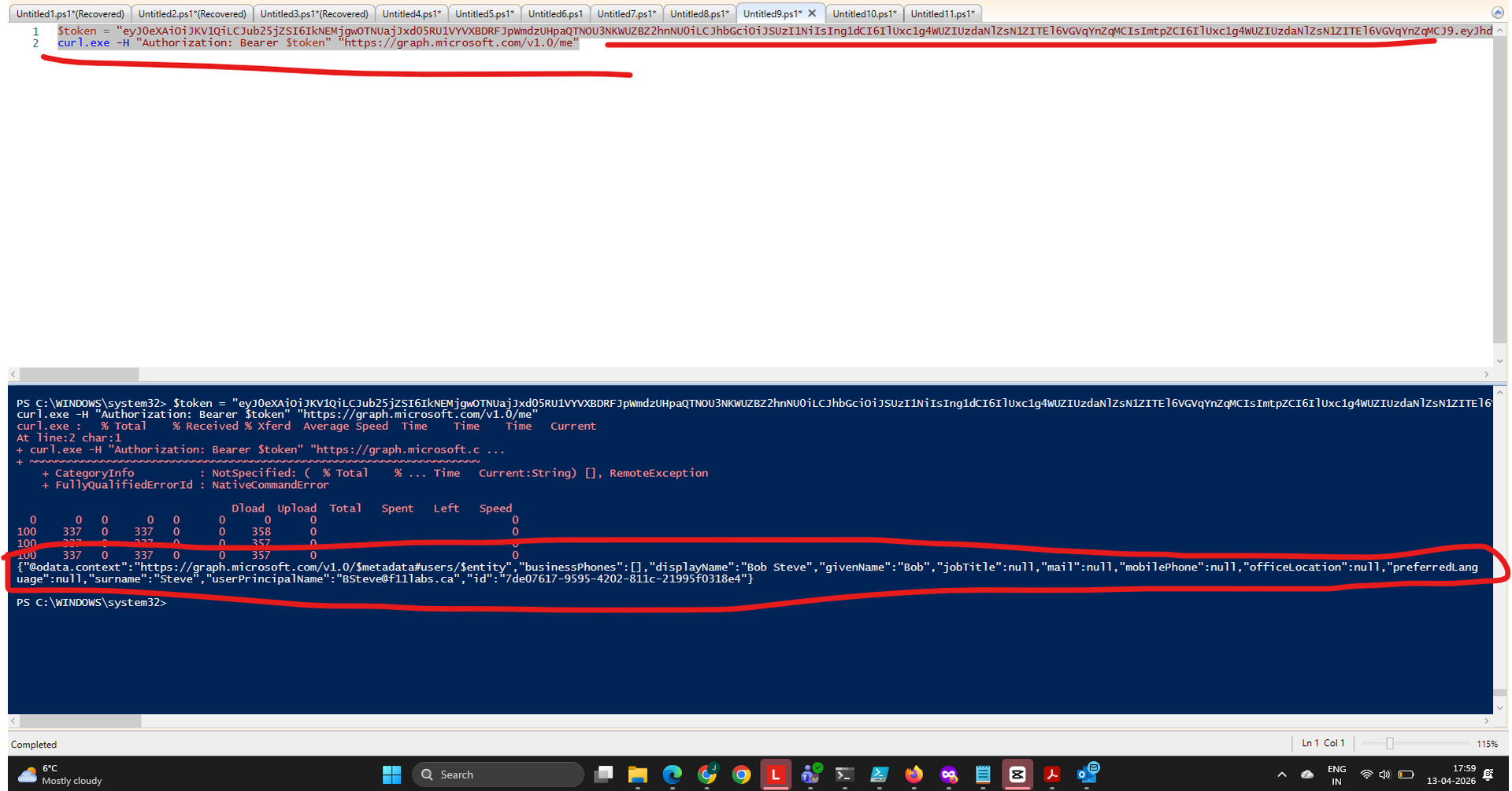
Evidence EID-EXP-016-04 – Data Access via Microsoft Graph API
Control Area: Data Access / Token Usage
Observation:
After consent was granted, access tokens were used to query Microsoft Graph API:
- Read user emails
- Access OneDrive files
Expected Secure State:
- Token usage should be monitored.
- Abnormal API access should trigger alerts.
- Conditional Access should evaluate app behavior.
Actual Result Data was accessed using delegated permissions without additional authentication prompts.
Impact:
- Exposure of unauthorized data
- Unnoticed access to emails and files
- No immediate alerts triggered.
Evidence Artifacts
Evidence Summary – OAuth Consent Phishing Risks
| 001 | Tenant Validation | Informational |
| 002 | App Registration | High |
| 003 | User Consent | Critical |
| 004 | Data Access | Critical |
Evidence-Based Conclusion
OAuth consent phishing exposes a critical identity security gap, as attackers exploit legitimate authentication and authorization flows rather than bypassing them.
This experiment demonstrates that:
- MFA does not prevent this attack
- No credentials are compromised.
- Users unknowingly grant access.
- Persistent access is achieved through tokens.
Without controls like disabling user consent, enforcing admin approval workflows, and monitoring apps, organizations remain vulnerable to data breaches.
Next Experiment
EID-EXP-017 – Suspicious OAuth Applications and Token Abuse Detection Gaps.
Related Analysis & Fix Guidance
- Technical deep dive: OAuth Consent Attacks in Microsoft Entra ID – Detection and Mitigation
- MSP risk & business impact: Silent Breaches via OAuth – Why MFA Is Not Enough
- Video walkthrough: OAuth Consent Phishing Explained | No Password, No MFA Attack